The post A review of HIPAA-compliant analytics platforms appeared first on Piwik PRO.
]]>SUMMARY
- In 2025, healthcare organizations face rigorous HIPAA compliance challenges, with increased enforcement resulting in substantial fines for violations, particularly when using non-compliant tools like Google Analytics, which cannot sign business associate agreements (BAAs) and risks exposing protected health information (PHI).
- Each healthcare organization needs to carefully assess the available analytics options, considering aspects like usability, resources, privacy and security, and analytics capabilities.
- HIPAA-compliant analytics platforms should provide features like customizable BAAs, robust data encryption, and secure hosting options to ensure compliance. On top of that, healthcare organizations should seek tools offering access to accurate data, flexible reporting and the ability to put data into action.
- Popular analytics tools like Adobe Customer Journey Analytics and Freshpaint provide HIPAA compliance but often involve high implementation costs, complex setups, or limitations like incomplete datasets due to aggressive PHI filtering.
- Platforms like Piwik PRO Analytics Suite offer a balance between strong privacy controls and actionable insights, allowing organizations to meet regulatory requirements without sacrificing analytics capabilities.
Collecting and analyzing user data is essential to healthcare businesses that want to build relationships with prospects, better meet their patients’ needs, and gain authority within the industry.
As a healthcare organization subject to HIPAA, you’re walking a fine line when trying to improve the patient experience and ensure your activities are HIPAA-compliant.
Since 2023, HIPAA enforcement has intensified, with over $100 million in fines for pixel tracking violations. Google Analytics remains dominant, but it’s fundamentally incompatible with HIPAA requirements.
In this article, we will show you the analytics vendors and implementations available on the market and explore their advantages and shortcomings concerning HIPAA compliance.
What are the challenges of finding a HIPAA-compliant analytics tool
HIPAA’s strict regulations require careful evaluation of analytics tools. Non-compliance risks heavy fines, with 47% of healthcare marketers reporting issues like reduced ROI and reputation damage.
As of 2025, HIPAA enforcement has surged, with fines up to $63,973 per violation and caps at $2M for repeat issues. In 2024, OCR closed 22 enforcement actions, followed by 10 more in 2025, targeting risk analysis failures.
When it comes to web analytics platforms and HIPAA, your approach depends on whether you collect protected health information (PHI) through your site or app. Data that isn’t considered PHI is outside the scope of HIPAA.
First, sharing PHI for marketing and analytics is not a permitted disclosure under the HIPAA Privacy Rule. To legally send PHI to your analytics platform, you must sign a business associate agreement (BAA) with the vendor, specifying each party’s responsibilities regarding PHI and ePHI and establishing a legally binding relationship.
Many vendors don’t want to sign BAAs. In this case, you must remove all identifiers from the data to use their services, so that it’s no longer considered PHI. But the process of de-identification is long and complicated.
For one thing, HIPAA views many types of URLs as PHI. It would be hard to de-identify all URLs, and doing so would make your analytics unusable. For example, de-identification would negatively impact remarketing and user-based or service-based reporting.
On the other hand, cherry-picking URLs containing PHI would also be difficult, mainly because of how much sites change over time.
If you need to comply with HIPAA, you should evaluate the available healthcare analytics solutions and find the right tool for your needs, even if it means migrating to a new vendor. Below, we will analyze how different vendors approach data privacy in healthcare and help you choose the best option for your organization.
Why Google Analytics isn’t HIPAA-compliant
Although Google Analytics remains widely used, numerous compliance concerns and recent enforcement actions have made GA4 unsuitable for healthcare organizations.
Let’s consider several ways to implement GA4 and explore the issues associated with each approach.
Client-side GTM and GA4
This setup is not HIPAA-compliant.
Why can’t you send protected health information (PHI) to Google
Organizations covered by HIPAA can’t disclose PHI to tracking technology vendors – this includes sharing and using PHI for marketing purposes. Google uses all data within its systems to develop new services, improve existing offerings, and create personalized advertising experiences. Using a covered entity’s PHI for Google’s scale of operations can be a severe violation of HIPAA’s Privacy Rule.
Google also stores all tracked data in databases located around the world and offers neither on-premise hosting nor bespoke data residency services. Thus, covered entities cannot control where their patient data is stored. HIPAA sees this as a breach of accountability.
Google’s position is unambiguous in their official documentation. According to Google’s Analytics Help Center, “Customers who are subject to HIPAA must not use Google Analytics in any way that implicates Google’s access to, or collection of, PHI”.
You must make an extra effort to avoid passing any trace of PHI to your analytics or switch to an analytics platform that will help you process patient data with the proper safeguards.
When using client-side GTM, the user’s browser communicates directly with third parties, making it challenging to control the shared information. Depending on how your website or app processes user information, there might be a risk of PHI being shared in HTTP requests.
What are the challenges of defining protected health information (PHI)
Not all health data is PHI. For example, phone numbers or IP addresses alone aren’t PHI, but they become PHI when linked to health conditions or treatments.
The HHS bulletin elaborates on when data may qualify as PHI. Healthcare information collected on a regulated entity’s website or app is generally considered PHI even if:
- The individual does not have an existing relationship with the regulated entity, and
- Data such as IP address or geographic location does not include specific treatment or billing information, like dates and types of healthcare services.
HHS guidance states that authenticated pages will likely contain many forms of PHI, making them subject to HIPAA.
It also clarifies when unauthenticated pages include PHI. Specifically, whether PHI is being disclosed depends on the underlying intentions of the visitor.
For example, if a student visited a regulated entity’s webpage to review its oncology service offerings for a research paper, the collection of identifying information on the student would not be a violation because it is not related to the student’s health care. On the other hand, if an individual visited the same oncology webpage to seek a second opinion on a cancer diagnosis, any identifying information collected would be PHI because it relates to the individual’s past, present, and/or future health.
The bulletin also mentions that mobile apps contain PHI provided by the app user and their devices, such as geolocation or device ID.
You can’t set GA4 tags on any pages that may fit the definitions provided in the HHS bulletin.
Note: In June 2024, a judge ruled in favor of the AHA, declaring that OCR had overstepped its authority when issuing the guidance. On August 29, the OCR decided not to appeal the district court’s decision.
The court ruling and HHS’ decision not to appeal it do not settle the issue of collecting and using PHI by healthcare organizations. The ruling was issued in a specific case, indicating that an IP address combined with visit data from an unauthenticated web page does not constitute PHI. However, the ruling does not vacate other parts of the guidance, like those relating to authenticated pages such as patient portals.
While the definitions of PHI and ePHI are well-established, the widespread use and interoperability of modern IT systems make it easy for PHI to inadvertently leak into your website or app. It’s wiser to stay on the safe side rather than rely on a gray-area interpretation of PHI. To protect patient privacy and reduce the risk of hefty fines, organizations must remain vigilant about the data they collect and share with analytics vendors.
Learn more about the implications of the court ruling: The AHA’s lawsuit against HHS guidance on online tracking technologies: What it means for HIPAA-covered entities and their use of analytics
Server-side GTM and GA4
This setup is not HIPAA-compliant.
Server-side GTM, when properly set up, helps you control what data you share with Google. User data is only sent to the server hosting the GTM container rather than being shared with multiple third-party servers. You can remove any PII within the server container before passing the data on to marketing partners.
However, you’ll face two types of issues with this implementation.
Why is it difficult to de-identify protected health information (PHI)
Since you’re not allowed to send PHI to Google Analytics, you must strip all PII/PHI from the data before sending it to GA4.
De-identifying PHI requires the removal of all 18 HIPAA identifiers (Safe Harbor method) or expert analysis (Expert Determination method) to ensure the data isn’t PHI and doesn’t fall under HIPAA’s Privacy Rule.
That said, it’s unlikely that you’ll be able to strip all PHI.
IP addresses and device IDs can be easily removed with ssGTM. However, URLs are more complicated to de-identify because you collect a URL title on every visit. The title can contain sensitive information, like the doctor’s name and specialization or a patient’s name, or you can collect search parameters in link decorations.
There are also issues with de-identifying custom dimensions, variables, and event attributes that you assign PHI to. For example, you may track a healthcare app and collect a custom event when someone clicks on a doctor’s image. The event collects the doctor’s name and specialization, which may lead to uncovering the individual’s health issue, thus making this data PHI.
What are the legal risks of using Google Tag Manager in healthcare
Another aspect concerns the legal risk involved with using GTM together with GA4.
This is reinforced by Google’s Tag Manager Use Policy, which explicitly states that users “will not assist or permit any third party to pass information, hashed or otherwise, to Google that Google could use or recognize as personally identifiable information”.
As a result, you can’t send PII to GA4, and PHI is a subset of PII.
Some people say that you can still safely analyze such data in GA4, and these terms don’t apply because:
- You can host ssGTM on the HIPAA-compliant infrastructure of your choice.
- If you de-identify data, it’s no longer considered PHI.
But there is a lot at stake here. As a HIPAA-covered entity, consult your legal team before implementing this option.
Find out more about Google Analytics and HIPAA: Is Google Analytics HIPAA-compliant?
ssGTM, BigQuery, and data visualization tool
This setup may be HIPAA compliant if you take certain steps.
Another option involves combining ssGTM with BigQuery and a data visualization tool.
This type of setup will only be affected by the ssGTM issue with the difficult de-identification process. But this problem can be mitigated when you work with a HIPAA-compliant data collection tool.
For example, you can set up ssGTM with different tech, including a data collection system, and transfer events directly into BigQuery. With this setup, the data would never be sent to Google Analytics servers and only be recorded in BigQuery, which is HIPAA-compliant. You can store the raw data and access it with a BI tool such as Looker Studio or Tableau.
Streaming events from ssGTM to BigQuery is simple but lacks analytics processing, requiring additional data handling in BigQuery.
Cons
- Loads of maintenance needed, which leads to inflated data team costs.
- De-identification will most likely be necessary with ssGTM, depending on downstream technologies’ compliance with HIPAA. It’s a complex and time-consuming process that requires stricter organizational measures.
- ssGTM lacks transparency – there is no way for end-users to monitor or make decisions about data processing.
Pros
- A lot of talent on the market is proficient at using Google’s products and can support your implementation.
- The setup with ssGTM and BigQuery is quite popular.
- You have the flexibility of your own data warehouse.
Adobe: Enterprise analytics solution
Adobe is the second-biggest enterprise analytics player on the market.
Adobe offers a few products that can help you improve healthcare experiences while protecting patient privacy:
- Adobe Analytics (AA) is an analytics and reporting solution that monitors user traffic and interactions across various marketing channels. AA offers customizable reporting, segmentation and predictive insights, but is complex, costly, and requires specialized expertise, limiting its accessibility.
- Adobe Customer Journey Analytics (CJA) lets you connect cross-channel data, explore the customer journey in full context and apply AI-driven insights, and it resembles GA4. Concerning HIPAA, CJA can easily identify and secure PHI and PII, apply access rules, and create data use audits.
- Adobe Launch is a tag management system and part of Adobe Experience Manager.
- Adobe Real-Time Customer Data Platform (CDP) connects customer data from all your channels into unified profiles that support discovering insights and delivering personalized experiences.
So, do Adobe’s products help you comply with HIPAA?
Providing PHI to Adobe is compliant only if it concerns a HIPAA-ready service, following the license agreement and BAA between Adobe and its client. To check which Adobe’s services are compliant, you can check this list of Adobe’s HIPAA-ready products.
Two analytics setups have been implemented on the market using Adobe’s products:
Adobe Launch and Adobe Analytics
This setup is not HIPAA compliant.
Adobe Analytics is not listed as HIPAA-ready on Adobe’s site. It means that Adobe won’t sign a BAA with you to use AA. As a result, you are not permitted to create, receive, maintain, or transmit PHI through Adobe Analytics.
Adobe Launch and Adobe Customer Journey Analytics
This setup is HIPAA compliant.
Adobe CJA is on the HIPAA-ready list, so you can safely use it as a HIPAA-covered entity and send PHI to it. This setup can be complemented with Adobe CDP for audience creation and activation.
However, since the only way to achieve HIPAA compliance with Adobe is by using CJA, note that this tool’s main advantage is integration with other components in the Adobe Experience Platform. By itself, CJA is far less advanced than AA.
It’s also worth noting that cost considerations are significant with Adobe solutions. Adobe’s enterprise analytics packages typically start at $48,000 annually, making it one of the more expensive options in the market.
Cons
- You are faced with high implementation and subscription costs.
- Adobe’s analytics products are difficult to learn and use.
- You risk single-vendor lock-in due to the amount of other tightly integrated products offered by Adobe.
Pros
- You can sign a BAA.
- You get an all-in-one analytics solution.
Piwik PRO: Full-featured HIPAA analytics
Piwik PRO has emerged as the leading HIPAA-compliant alternative to Google Analytics, purpose-built for organizations operating in highly regulated industries. Piwik PRO provides privacy-friendly analytics and combines accuracy, flexibility, and complete control when collecting and analyzing customer data.
Unlike other vendors that add compliance features later on, Piwik PRO was designed from the ground up with privacy and security requirements in mind, including HIPAA-related features and controls. Piwik PRO also helps you comply with the HHS bulletin on the use of tracking technologies. Because of that, we can easily support your analytics use cases in healthcare.
Here is an overview of our modules, all of which allow you to comply with HIPAA:
- Analytics allows you to analyze the customer journey across websites and apps. You can use advanced analytics features like funnels, user flows, customizable reports and dashboards. And you can always extend the platform’s capabilities through custom development and integrations. You can use raw data exports to send data to any destination. Increased security features allow you to use Analytics in sensitive industries, like healthcare.
- Tag Manager lets you quickly create, test, and deploy tags from customizable templates. You gain greater flexibility in collecting and utilizing their data through smooth integration with other Piwik PRO modules.
- Customer Data Platform (CDP) enhances your ability to act on the insights you draw from your data. You can better understand your customers, provide more personalized experiences, and improve your campaigns.
- Consent Manager is an optional addition for increased transparency, allowing you to collect, manage, and store user consents.
Key HIPAA compliance features
The most important features of Piwik PRO that support HIPAA compliance include:
- Ability to sign a customizable business associate agreement (BAA), allowing you to send all types of PHI to your analytics setup.
- Hosting on HIPAA-compliant Microsoft Azure data centers, where you can choose the specific location of your data.
- ISO 27001 and SOC 2 type II certifications.
- Encryption of ePHI when the data is at rest and in transit.
- Advanced user-permission options that let you put PHI only in the hands of authorized personnel.
- Not sharing ePHI with third parties or reusing it for other purposes.
- Regular privacy and security audits undertaken by external, independent bodies to ensure the highest level of security measures.
You don’t have to choose between compliance and effective insights in healthcare
Schedule a demo to see how Piwik PRO’s HIPAA-compliant analytics can streamline your data strategy:
Implementation options
Recommended ways for you to implement Piwik PRO modules include:
Piwik PRO Analytics, Tag Manager and CDP
This setup is HIPAA-compliant and provides a complete suite of modules for effective healthcare analytics.
With this option, you can safely collect and analyze PHI and ePHI while respecting the highest privacy and security safeguards. You can analyze the customer journey across all channels, control data collection and adjust it to your needs, and you get to activate the data to improve the patient experience.
Piwik PRO Analytics Suite and a data warehouse
This setup is HIPAA-compliant.
This is a point solution for marketers, combining the capabilities of analytics and activation. You can connect our suite of products with a data warehouse via scheduled raw data exports or API, allowing you to extend the platform’s data analysis functionalities.
Learn more about How to make your website compliant with HIPAA using Piwik PRO.
Cons
- You are using tools from one vendor only.
- There is a client-side tag manager.
Pros
- You can sign a BAA.
- You get an all-in-one analytics solution.
- The costs are low.
- CDP is available for server-side profile activations.
- You have the ability to use Piwik PRO as an analytics endpoint in server-side tracking, which improves data collection, accuracy and control.
- The modules are easy to learn and use thanks to their similarity to the Universal Analytics interface.
Freshpaint: Healthcare Privacy Platform
This setup is HIPAA-compliant but has limitations.
Freshpaint offers its Healthcare Privacy Platform, which serves as a privacy layer between your website and analytics tools.
It captures all tracking data and automatically de-identifies PHI before sending cleaned data to downstream tools. While this approach allows continued use of familiar platforms, it comes with significant trade-offs.
Freshpaint is not an analytics platform itself and must be connected to other tools to create a full analytics setup. Setup and maintenance require significant technical skills, resources, and coordination across multiple teams, which makes using the tool very costly.
You also can’t report on or visualize the data within Freshpaint’s platform, meaning you won’t have access to PHI. As a result, your dataset will be incomplete and therefore not fully accurate.
Cons
- Not a complete analytics platform – requires additional tools for full functionality
- Complex setup and maintenance requiring specialized technical expertise
- Higher total cost when factoring in multiple vendor relationships
- Limited reporting capabilities within Freshpaint itself
- Data accuracy issues due to aggressive PHI filtering
- Ongoing compliance risk if de-identification fails
Pros
- Enables the use of the existing Google Analytics setup
- Healthcare-specific BAA and compliance features
- Advanced PHI detection and filtering capabilities
Using a mix of vendors
This setup may be HIPAA compliant if you take certain steps.
Combining tools from different vendors can get complex. You need to assess your needs very well, understand what each tool offers, and check how it can help you comply with HIPAA.
Generally, your analytics setup should include the following tools:
Data collection system + data warehouse + data visualization tool
We list some popular data collection systems below and link to the relevant information regarding their HIPAA compliance. Aside from that, you will need to verify their specific HIPAA compliance yourself.
Data collection system
Data collection tools like CDPs (e.g., Segment) and BDPs (e.g., Snowplow) vary in complexity and offered capabilities. These vendors offer more than just pure tracking, meaning you need to make a separate assessment of your needs and how these tools fulfill them.
Popular data collection systems (trackers or CDPs) that will sign a BAA:
- Rudderstack
- Tealium
- Segment
- Snowplow – no need for a BAA in the self-hosted version (it’s uncertain whether the vendor would sign a BAA for the cloud)
Data warehouse
A data warehouse holds data that is extracted, loaded, and transformed from one or more operational source systems and modeled to enable data analysis and reporting in your business intelligence (BI) tools.
Popular data warehouse providers that will sign a BAA:
- Snowflake
- Google Cloud Platform (such as Google BigQuery)
- Microsoft Azure (such as Microsoft Azure Data Synapse)
- Amazon Web Services (such as Amazon Redshift)
Data visualization tool
A data visualization tool enables the visual representation of data, allowing for the effective extraction of actionable insights from the data.
Popular data visualization tools that will sign a BAA:
Common setups that include different vendors:
- Piwik PRO (data collection, visualization, and CDP) + data warehouse (data copy for science team) + Looker Studio or Tableau (broad data visualization)
- Adobe CJA + CDP + AEP (data collection, activation, and visualization)
- Rudderstack (data collection, CDP) + data warehouse + data visualization tool
Most data collection vendors, such as Freshpaint, allow for GA4 as a destination, so the flow can also look like this:
A data collection system + GA4
However, this setup requires you to de-identify PHI to safely use it.
Cons
- You need to review the HIPAA compliance of each vendor – analyze security and privacy, manage and negotiate cooperation with all three selected vendors, sign a BAA with each of them, etc.
- The connection between the systems may not be seamless – changes or API updates in each of those vendors may break your setup.
- You would require a data analyst or database expert to manage and maintain pipelines.
- The costs are very high – you need to pay for implementation, licensing of multiple vendors, and maintenance.
Pros
- You benefit from diversification of vendors, meaning no vendor lock-in.
- You can combine the benefits and features of each system you implement.
How to choose the right HIPAA-compliant analytics platform
As of 2025, the choice is no longer whether to replace Google Analytics, but which HIPAA-compliant alternative to choose. With enforcement at record levels and mature alternatives available, healthcare organizations that continue using Google Analytics are taking unnecessary legal and financial risks.
Here is a breakdown of key features of the recommended HIPAA-compliant analytics tools that we’ve looked into:
| Piwik PRO | Adobe CJA | Freshpaint | Mix of vendors | |
|---|---|---|---|---|
| HIPAA compliance | ||||
| Ease of implementation | ||||
| Secure data handling for organizations in sensitive industries | ||||
| Cost | $ | $$$ | $$ | $$$ |
| Data ownership | Adobe ecosystem | Limited | ||
| Support quality | ||||
| Built-in analytics capabilities | ||||
| Integrations with other tools |
Compared to other options for analytics in healthcare, Piwik PRO offers the optimal balance of HIPAA compliance, enterprise features, and affordability, with a Google Analytics-like interface for seamless adoption.
Healthcare marketing insights that transform your business and keep you HIPAA-compliant
No more compromises between accurate data and privacy – learn why industry leaders choose Piwik PRO:
Frequently asked questions (FAQ) about healthcare analytics platforms
Can I use server-side Google Tag Manager with BigQuery safely for HIPAA compliance?
Yes, BigQuery can be HIPAA compliant with a signed BAA, but the challenge lies in the server-side GTM de-identification process. You’ll face significant technical hurdles removing PHI from URLs, custom dimensions, and event parameters before data reaches BigQuery. The setup requires ongoing maintenance and carries compliance risks if de-identification fails. Most healthcare organizations find dedicated HIPAA-compliant platforms more reliable and cost-effective long-term.
What specific data gets classified as PHI that I might accidentally send to Google Analytics?
Beyond the obvious patient names or medical record numbers, common PHI in analytics includes: URL parameters containing appointment IDs or doctor names, page titles with patient-specific information, custom events tracking interactions with doctor profiles, search terms entered on health condition pages, and form field data from appointment booking. Even data like “clicked on Dr. Smith’s cardiology page” combined with an IP address can constitute PHI.
Can I safely use Google Analytics now that the HHS guidance was ruled unlawful by the court?
No. The June 2024 court ruling was very specific – it only addressed IP addresses on unauthenticated pages where visitor intent couldn’t be determined as health-related. The ruling explicitly did NOT address authenticated pages (like patient portals), pages with clear health intent, or other forms of PHI collection. Google still refuses to sign BAAs, making compliance impossible for most healthcare analytics use cases.
Do I need to de-identify data for HIPAA-compliant analytics tools?
No, one of the major advantages of truly HIPAA-compliant platforms is that you don’t need to de-identify PHI before sending it to them. Platforms like Piwik PRO that sign BAAs can legally receive and process PHI. This eliminates the complex and error-prone de-identification process required for non-compliant platforms like Google Analytics.
What should I do if my current analytics vendor won’t sign a BAA?
If your current vendor refuses to sign a BAA, you have limited options:
- Stop sending PHI to that platform (often impractical for healthcare sites)
- Implement data de-identification (complex and error-prone)
- Switch to a compliant alternative (recommended approach)
- Use an intermediary solution like Freshpaint (adds complexity and cost)
The cleanest solution is typically migrating to a platform designed for healthcare compliance.
Can I use multiple analytics platforms simultaneously?
Yes, but with considerations. You can run compliant analytics alongside other platforms, but ensure that any platform receiving PHI has a signed BAA. Some organizations use compliant analytics for authenticated/sensitive pages and standard analytics for purely informational content. However, managing multiple platforms increases complexity and costs – a single compliant solution across your entire digital presence is often more efficient.
The post A review of HIPAA-compliant analytics platforms appeared first on Piwik PRO.
]]>The post HIPAA-compliant analytics in 2025: Your complete vendor comparison and selection guide appeared first on Piwik PRO.
]]>SUMMARY
- Healthcare organizations paid over $100 million in HIPAA fines between 2023-2025 due to pixel tracking violations, with individual penalties now reaching up to $2.1 million for willful neglect.
- Google Analytics is fundamentally incompatible with HIPAA requirements because Google won’t sign a business associate agreement (BAA) and explicitly prohibits healthcare organizations from sharing PHI through their platform.
- Even unauthenticated healthcare websites can violate HIPAA if they collect data like IP addresses or track visits to health-related pages, as this information can be considered protected health information (PHI).
- Several mature HIPAA-compliant alternatives now exist, including Piwik PRO, Adobe Customer Journey Analytics, and specialized platforms like Freshpaint, each offering BAAs and healthcare-specific security features.
Collecting and analyzing user data is essential to healthcare businesses seeking to build relationships with prospects, better meet their patients’ needs, and gain authority within the industry.
However, in 2025, HIPAA enforcement has expanded beyond internal systems and EHRs to include what happens in users’ browsers, making compliance more complex than ever. As a healthcare organization subject to HIPAA, you’re walking a fine line when trying to improve the patient experience while ensuring your activities remain compliant.
Vendors have been adjusting to the shifting landscape of privacy-oriented analytics and their clients’ expectations. Many of them change their offers accordingly.
At the same time, the dominant analytics vendors are not necessarily the most compliant options for healthcare providers. The stakes have never been higher, with U.S. healthcare firms paying over $100 million in fines between 2023 and 2025 due to pixel tracking violations.
In this article, we will explain why finding a HIPAA-compliant analytics provider should be a top priority and outline the key factors to consider when selecting your vendor. We will also compare popular analytics vendors, examining their advantages and capabilities in terms of HIPAA compliance.
Current enforcement landscape and recent developments
The HIPAA compliance landscape for analytics has evolved dramatically in recent years. Here is a breakdown of the most important developments:
Updated penalty structure
HIPAA fines in 2025 range from $137 to $63,973 per violation for unknowing violations, with annual caps reaching $2,000,000 for repeat violations. There are four tiers of penalty structures, with the highest one concerning uncorrected willful neglect reaching $2,134,831 in 2024. Just last year, Montefiore Medical Center faced a $4.75 million penalty and a two-year corrective action plan after potential security rule violations.
AHA court victory
In June 2024, a US district court ruled in favor of the American Hospital Association’s lawsuit against HHS guidance on online tracking technologies. On August 29, the OCR decided not to appeal the district court’s decision. However, the victory’s scope is more limited than many healthcare organizations initially believed.
The ruling only invalidates the part of the guidance stating that combining an IP address with a visit to a general health information page constitutes PHI. Other parts of the ruling, such as those relating to authenticated pages, including patient portals, remain valid.
Additionally, HHS can enforce certain instances of combining HIPAA identifiers with health information, for example, an ad click ID connected with a scheduled doctor appointment shared with an ad platform like Google.
Tracking pixels on major hospital websites
The Markup investigated the top 100 hospitals in the US and discovered tracking technologies on the appointment scheduling pages of 33 hospitals, meaning they were sending appointment data to Facebook, along with users’ IP addresses.
Two lawsuits were immediately filed against Meta and health systems, including the University of California San Francisco and Dignity Health. This investigation revealed the widespread nature of non-compliant practices across major healthcare institutions.
It sparked a wave of litigation that continues today, with healthcare organizations facing class action lawsuits for using tracking pixels.
Increased HIPAA enforcement
OCR has launched two enforcement initiatives in recent years – one targeting noncompliance with the HIPAA Right of Access in 2019, and the more recent focusing on noncompliance with the risk analysis provision of the HIPAA Security Rule. OCR Director confirmed that 22 enforcement actions were closed by OCR in 2024 with either settlements or civil monetary penalties, making it one of the busiest years for HIPAA enforcement.
This year has also begun with a large number of financial penalties, with a further 10 announced by the end of May 2025.
Beyond financial penalties, malpractice involving healthcare data can also damage patients’ trust and affect their relationship with their healthcare provider.
The Federal Trade Commission (FTC) involvement
The Federal Trade Commission has issued orders in several cases relating to healthcare providers, including ordering the telehealth company Cerebral to pay a $7 million fine and limit the use of consumer health data for advertising purposes.
The April 2024 ruling establishes precedent for how the FTC will address healthcare data misuse in the digital advertising space. A common legal basis for the FTC’s involvement is the FTC Act, which prohibits unfair or deceptive trade practices. Consequently, even if an organization isn’t directly covered by HIPAA, it may still face federal oversight for the misuse of healthcare data.
The challenge of finding a HIPAA-compliant analytics platform
Healthcare organizations seeking analytics solutions face a complex landscape of regulatory requirements, technical limitations, and vendor constraints that make compliance particularly challenging.
Signing a business associate agreement (BAA)
When it comes to web analytics platforms and HIPAA, your approach depends on whether you collect protected health information (PHI) through your site or app. Data that isn’t considered PHI is outside the scope of HIPAA.
To legally send PHI to your analytics platform, you must sign a business associate agreement (BAA) with any vendor matching the definition of a business associate. A BAA specifies each party’s responsibilities regarding PHI and ePHI and establishes a legally binding relationship.
Many vendors don’t want to sign BAAs because doing so would make them directly liable for compliance with certain HIPAA provisions, requiring them to implement comprehensive security measures.
It’s vital to accurately identify which vendors and partners qualify as business associates under HIPAA. Some relationships may seem less directly related to healthcare operations, but they still involve access to PHI. Watch out for unnecessarily entering into BAAs with other HIPAA-covered entities or third-party service providers who have no access to PHI.
PHI de-identification
If your business associate, such as an analytics vendor, doesn’t offer a BAA, you must remove all identifiers from the data to use their services, so that it’s no longer considered PHI. HIPAA’s Privacy Rule provides two de-identification methods for health information: Expert Determination and Safe Harbor. De-identified data created following these methods does not fall within the definition of PHI.
The process of de-identification is lengthy and complex, presenting numerous technical and practical challenges.
Even on unauthenticated webpages, your website can be in violation of HIPAA if it gathers information that may contain PHI. This creates practical challenges because, even without a login, tracking an IP address or geolocation on these pages can be considered PHI, as it suggests an individual’s interest in a specific healthcare condition or service.
It’s unlikely that you’ll be able to strip all PHI. Healthcare organizations face particular challenges with:
- IP addresses and device IDs that can be removed, but leave gaps in analytics capabilities
- URL titles that can contain sensitive information, like doctor names and specializations
- Custom tracking events that may inadvertently collect PHI through standard analytics implementations
Additionally, de-identifying all URLs would limit the usability of your analytics. De-identification would negatively impact remarketing and user-based or service-based reporting. On the other hand, cherry-picking URLs containing PHI is nearly impossible, given the dynamic nature of data collected and processed by websites and platforms.
The evolving analytics landscape presents both opportunities and challenges for healthcare organizations. Recent developments in privacy-focused analytics platforms, server-side tracking solutions, and healthcare-specific analytics tools have created new options for organizations seeking HIPAA-compliant alternatives.
With increased regulatory scrutiny and evolving technology, healthcare organizations must take a proactive approach to analytics compliance. This includes conducting regular audits of all digital tracking technologies, implementing robust data governance frameworks, and staying current with emerging privacy regulations that may impact analytics practices. The cost of non-compliance has never been higher, making it essential to invest in proper HIPAA-compliant analytics solutions.
Is Google Analytics HIPAA-compliant?
The analytics landscape has matured significantly since Google completed its transition from Universal Analytics to GA4 in July 2023. Google Analytics remains the most widely used enterprise analytics platform.
However, following the 2022 HHS guidance on the use of tracking technologies, Google Analytics is no longer recommended for use in the healthcare industry.
Google offers its marketing technologies for free because it gets access to data collected by businesses that implement its services. The tech giant uses data within its systems to develop and improve its services and personalize their advertising experience. This business model is fundamentally incompatible with HIPAA requirements.
Google does not offer a business associate agreement (BAA), meaning you can’t share PHI with them. Google also explicitly forbids customers subject to HIPAA from using Google Analytics and sharing PHI with them.
Find out more about Google Analytics and HIPAA: Is Google Analytics HIPAA-compliant?
Is Adobe Analytics HIPAA-compliant?
Adobe has a list of HIPAA-ready services, but only certain products are compliant. To check which of Adobe’s services are compliant, you can check this list of Adobe’s HIPAA-ready products.
- Adobe Analytics is not listed as HIPAA-ready on Adobe’s site. It means that Adobe won’t sign a BAA with you to use AA, and you can’t collect or share PHI through Adobe Analytics.
- Adobe Customer Journey Analytics (CJA) is on the HIPAA-ready list, so you can safely use it as a HIPAA-covered entity and send PHI to it.
Find out more about Adobe Analytics and HIPAA: Is Adobe Analytics HIPAA-compliant?
Popular HIPAA-compliant analytics platforms
The healthcare analytics landscape has undergone a fundamental shift. Many analytics tools still cannot adequately address HIPAA compliance requirements and don’t sign BAAs. However, this shift also presents opportunities – HIPAA-covered organizations have a chance to reassess the tools they use for analytics and marketing, and futureproof their compliance.
The market for HIPAA-compliant analytics has matured significantly, offering healthcare organizations various options to meet their analytical needs while maintaining regulatory compliance.
Let’s review some popular analytics options that can meet the needs of healthcare organizations.
Piwik PRO Analytics Suite
Piwik PRO Analytics Suite is a privacy-focused analytics and data activation platform that helps businesses collect, analyze, and put user data into action. The platform is tailored for industries with strict data compliance requirements, such as healthcare, and enables them to enhance their marketing effectiveness and deliver better user experiences.
Key strengths:
- HIPAA compliance with the ability to sign a customizable BAA
- Strong data ownership and governance tools
- Data encryption in transit and at rest, secure HIPAA-compliant hosting with Microsoft Azure, advanced anonymization options, granular access controls and more
- Comprehensive suite including analytics, tag management, consent management, and customer data platform
- ISO 27001 and SOC 2 certifications, including a HIPAA compliance assessment
- Competitive pricing and access to support & implementation services
- Ability to combine strong privacy compliance with effective analytics and data activation capabilities
Best for:
Organizations seeking an all-in-one platform with high data autonomy, configurable privacy settings, and seamless compliance with HIPAA and other regulations such as GDPR and CCPA.
Adobe Customer Journey Analytics (CJA)
Adobe Customer Journey Analytics (CJA) enables you to connect and normalize cross-channel data into actionable profiles, explore the customer journey in its full context, and apply AI-driven insights to deliver personalized experiences at scale.
Key strengths:
- Adobe CJA can identify and secure PHI and PII, apply access rules, and create data use audits to handle patient data
- The platform uses AI and machine learning to offer real-time insights into customer journeys, helping healthcare providers understand and optimize their patients’ experiences
- Strong integration with Adobe Experience Platform
Best for:
Large organizations with existing Adobe infrastructure and the technical expertise to implement the platform and fully leverage its capabilities.
Matomo
Matomo is an open-source analytics platform that can be self-hosted to support HIPAA compliance. While it provides full control over data, the task of maintaining compliance, including secure hosting and audit logging, falls entirely on the user.
Key strengths:
- Self-hosted option allows HIPAA-compliant configurations
- No data sampling, full data ownership
- Limited out-of-the-box support for enterprise security standards
Best for:
Organizations with technical resources to manage and secure their own analytics infrastructure.
Mixpanel
Mixpanel offers product analytics with HIPAA-compliant options through a separate agreement and an enhanced security tier. Its event-based tracking is ideal for understanding user behavior within digital applications.
Key strengths:
- HIPAA-compliant plans available on request
- Powerful segmentation and retention analysis
- Modern UX with flexible dashboards
Best for:
Healthcare product teams focused on app engagement and retention metrics.
Amplitude
Amplitude is a product analytics platform designed for in-depth behavioral insights across digital experiences. It offers a HIPAA-compliant plan with enhanced security, making it suitable for healthcare and life sciences companies that handle PHI. Amplitude’s strength lies in its robust analytics capabilities, such as cohort analysis, retention tracking, and real-time collaboration.
Key strengths:
- HIPAA-compliant enterprise tier available upon request
- Advanced behavioral analytics, funnels, and retention tracking
- Built-in identity resolution and user journey mapping
- Scalable architecture with real-time event ingestion
- SOC 2 Type II and ISO 27001 certifications
Best for:
Healthcare organizations and digital health startups that need granular product insights to optimize patient or user engagement without sacrificing compliance.
Heap Analytics
Heap provides automatic data capture, making it easy to analyze user behavior without manually setting up event tracking. HIPAA compliance is available on select enterprise plans, featuring security protocols including data encryption, access controls, and audit logs.
Key strengths:
- HIPAA-compliant deployment available on request, including a BAA
- Advanced retroactive analysis and journey visualizations
- Automatic event capture that reduces implementation complexity
- ISO 27001 and SOC 2 certifications
Best for:
Teams seeking rapid setup and detailed behavioral analytics with minimal developer input – ideal for growth and product teams in HIPAA-regulated environments.
Freshpaint
Freshpaint is a healthcare-focused tool that functions as a filter routing data to analytics and marketing tools while providing a strict layer of privacy controls and compliance enforcement. It’s not an analytics platform in itself and doesn’t offer reporting or visualization options – it must be connected to other tools to create a full analytics setup.
Key strengths:
- Built for HIPAA compliance – BAA signed by default
- Real-time data routing with automatic PHI filtering
- Visual tagging interface for non-technical users
- Consent enforcement across third-party tools
- SOC 2 Type II and HITRUST CSF certification
Best for:
Healthcare and health tech companies with the resources and skills to implement a plug-and-play analytics integration layer that ensures downstream compliance and simplifies consent governance.
COMPARISON
The comparison of 9 HIPAA-compliant web analytics platforms
Compare the main features of Piwik PRO, Freshpaint, Matomo, Mixpanel, Amplitude, Heap, Tealium, Adobe CJA and Piano Analytics.
Best practices for selecting a HIPAA-compliant analytics vendor
The ideal HIPAA-compliant analytics platform depends on specific organizational needs, technical capabilities, and resource constraints. Organizations seeking comprehensive functionality with minimal complexity may prefer integrated solutions that provide complete analytics suites with built-in compliance features. Those with specific technical requirements or existing tool investments might benefit from platforms that offer flexibility and integration capabilities.
The key is matching platform capabilities with organizational requirements while ensuring robust compliance measures that protect patient data and support long-term analytical goals. Success depends not just on the platform choice but on proper implementation, ongoing maintenance, and adherence to evolving regulatory requirements.
Here are key aspects to consider when choosing the right HIPAA-compliant analytics provider:
Essential compliance requirements
1. Business associate agreement (BAA)
- Ensure the vendor will sign a comprehensive BAA covering all required services and data types.
- Check that the BAA includes specific provisions for data processing, storage, and transmission.
- Verify that the BAA includes breach notification and incident response procedures.
2. Data hosting and residency
- Confirm data is hosted in a HIPAA-compliant infrastructure with proper certifications.
- Evaluate data residency options, including the ability to choose specific geographic locations.
- Verify that encryption standards for data at rest and in transit meet HIPAA requirements.
3. Security certifications
- Look for SOC 2 Type II certification as a baseline security standard.
- Learn if the vendor holds ISO 27001 compliance, which demonstrates a comprehensive approach to security management.
- Consider vendors that undergo regular third-party audits.
Technical evaluation criteria
1. PHI handling capabilities
- Identify whether the platform automatically collects and protects standard PHI, such as IP addresses and page URLs.
- Evaluate built-in data minimization features that limit PHI collection to necessary elements only.
- Look for robust data retention management tools with automated deletion capabilities.
- Determine if the platform provides granular access controls to limit the exposure of PHI to authorized personnel.
2. Integration and implementation
- Assess the complexity of the migration from your existing tools, such as Google Analytics.
- Find out what pre-built integrations are available, including connectors to popular healthcare technology tools.
- Discover the available customer support, onboarding, and implementation services.
3. Reporting and analytics features
- Verify if the platform provides the specific healthcare metrics your organization requires.
- Learn what advanced features are available – for example, funnel analysis, custom reporting, customizable dashboards and others you need.
- Determine the options available for extending platform capabilities, such as data exports or custom development.
Vendor assessment framework
1. Financial considerations
- Consider the total cost of ownership, including potential integration costs with existing systems.
- Factor in implementation costs, training, and ongoing support.
- Consider vendors that provide good value through all-in-one solutions to reduce costs.
Google Analytics is free, so healthcare organizations should expect to pay more for a HIPAA-compliant analytics solution.
2. Risk management
- Ensure the vendor doesn’t share data with third parties or reuse it for other purposes.
- Find out if the vendor provides regular security updates and proactive compliance monitoring.
- Assess incident response and breach notification procedures.
- Factor in whether the vendor prioritizes healthcare clients and understands industry-specific needs.
3. Scalability and futureproofing
- Determine if the vendor offers modular functionality, such as analytics, tag management, and CDP capabilities, within a single platform.
- Assess the solution’s scalability to determine how well it can grow in line with your organization’s increasing data volume and complexity.
- Learn how the vendor stays current with evolving HIPAA requirements.
The path forward
Despite numerous challenges, healthcare organizations are finding ways to maintain effective analytics while ensuring compliance with regulations. There are solutions for healthcare providers and organizations that want to run a modern digital business with all the necessary marketing tools to optimize and grow.
Healthcare providers must invest in compliant vendors and establish a compliance strategy to unlock the full potential of data-driven marketing, analytics, and advertising while safeguarding patient privacy.
The challenge of finding HIPAA-compliant analytics platforms reflects the broader transformation of healthcare digital marketing in the post-2022 regulatory environment. Organizations that successfully navigate these challenges will be those that prioritize compliance from the outset, invest in specialized solutions, and maintain ongoing vigilance as regulations continue to evolve.
HIPAA compliance doesn’t have to limit your marketing or analytics activities. Piwik PRO provides healthcare institutions with actionable marketing insights, ensuring regulatory compliance, and securing patient data.
Learn more about how Piwik PRO can support your organization in HIPAA-compliant analytics:
The post HIPAA-compliant analytics in 2025: Your complete vendor comparison and selection guide appeared first on Piwik PRO.
]]>The post The comparison of 9 HIPAA-compliant web analytics platforms appeared first on Piwik PRO.
]]>Choosing a platform that doesn’t match your needs or available resources can put sensitive patient information at risk, leading to costly compliance violations and loss of patient trust. As a healthcare organization, you must consider privacy and security-related aspects, such as security protocols, certifications, data protection and anonymization features, hosting options, and regulatory compliance. At the same time, your selected platform should meet your expectations in terms of usability, product capabilities, data integration options, analytics, and reporting features, and others.
In this comparison, we will analyze the leading HIPAA-compliant web analytics platforms, including Piwik PRO, Freshpaint, Matomo, Mixpanel, Amplitude, Heap, Tealium, Adobe Customer Journey Analytics and Piano Analytics. We will cover essential criteria such as data security, encryption standards, business associate agreements (BAAs), integration capabilities, hosting options, data anonymization features, reporting and analytics features, customer support options, and much more.
By understanding how these platforms stack up, you’ll be better equipped to select a solution that not only meets your compliance requirements but also allows your organization to turn healthcare data into actionable insights.
COMPARISON
The comparison of 9 HIPAA-compliant web analytics platforms
Compare the main features of Piwik PRO, Freshpaint, Matomo, Mixpanel, Amplitude, Heap, Tealium, Adobe CJA and Piano Analytics.
How to find the right HIPAA-compliant web analytics platform for your healthcare organization
For each platform, we outline and compare features from the following categories:
General overview
The first section includes an overview of each platform’s HIPAA compliance status, privacy and security measures, available plans, pricing, and product capabilities. This helps you quickly understand the overall suitability of the solution for your needs.
Data privacy and security
Data privacy and security features directly impact how protected health information (PHI) is handled. Key elements such as data control, the availability of business associate agreements (BAAs), regulatory compliance adherence, access controls, audit logs, server-side tagging, encryption, anonymization, hosting environment, backups, security certifications, and integration with consent management systems collectively ensure that patient data is protected against unauthorized access and breaches.
Data collection flexibility
Data collection flexibility determines how different platforms accommodate the diverse technical environments and tracking requirements of healthcare organizations. The availability of JavaScript tags and software development kits (SDKs), support for custom variables and dimensions, data freshness and retention policies, and the number of properties or custom domains that can be tracked show how well the platform can capture relevant user interactions without compromising compliance.
Data processing and connectivity
Data processing and connectivity features such as raw data access, reporting APIs, data sampling methods, and integrations with business intelligence (BI) and data visualization tools enable healthcare organizations to analyze data effectively and integrate analytics insights into broader decision-making workflows. The availability of direct integrations with a customer data platform (CDP) and tag manager further enhances the ability to comprehensively manage and activate patient data.
Reporting features
Reporting features determine how well healthcare teams can derive insights from the collected data. In this section, we outline features like access to detailed reports and metrics, customizable dashboards, event and goal tracking, funnel and product analytics, user flow visualization, session logs, real-time data, calculated metrics, automatic insights, and user-level reporting.
Support and customer care
Support and customer care options play a vital role in successful platform adoption and ongoing compliance. Basic support, such as help centers, community forums, and email assistance, provides foundational help, while more extensive services, like dedicated support specialists, personalized implementation, and onboarding, ensure that organizations can tailor the platform to their specific HIPAA requirements and operational needs.
Overview of web analytics vendors offering HIPAA compliance
Our comparison includes the following vendors:
Tealium
Tealium is an enterprise customer data platform and tag management leader, specializing in secure, compliant, and real-time customer data management across large organizations. With certifications such as HIPAA, ISO 27001, and SOC 2, plus private cloud hosting options, Tealium is tailored for large organizations with complex data governance and compliance requirements. It is the best fit for enterprises needing granular control over customer data and seamless integration across multiple channels.
Adobe Customer Journey Analytics (CJA)
Adobe CJA is an enterprise analytics solution designed to unify and analyze customer journeys across multiple channels in real time. Integrated deeply within the Adobe Experience Cloud, CJA provides advanced segmentation, visualization, and reporting capabilities while maintaining strong privacy and compliance controls, including HIPAA readiness. It is particularly well-suited for large enterprises that require comprehensive cross-channel insights and already leverage Adobe’s ecosystem for marketing and customer experience management.
Piano Analytics
Piano Analytics (formerly AT Internet) is a European-focused analytics platform that emphasizes privacy, compliance, and actionable digital insights. It supports GDPR compliance and flexible data hosting options, providing detailed web and product analytics along with segmentation and reporting features. Piano Analytics is ideal for organizations in Europe or those with stringent privacy requirements seeking a robust analytics solution tailored to digital content and marketing performance.
Mixpanel
Mixpanel is an advanced product analytics tool offering interactive dashboards and experimentation tools that empower product managers and marketers to optimize user engagement and feature adoption. It provides real-time event tracking, cohort analysis, and user segmentation, helping product and marketing teams optimize patient engagement and retention while maintaining compliance. Mixpanel is a good fit for healthcare SaaS and digital health companies that need actionable behavioral analytics combined with HIPAA safeguards.
Matomo
Matomo is an open-source web analytics platform. It was founded in 2007 and was known as Piwik until 2018, when it rebranded. Matomo enables organizations to control their analytics data while complying with GDPR and other privacy regulations. Its customizable dashboards, heatmaps, and session recordings provide rich insights into user behavior. Because there is no option to sign a BAA, HIPAA-covered organizations need to self-host their analytics if they choose Matomo. The platform is suitable for companies seeking an open-source alternative to mainstream analytics tools.
Amplitude
Amplitude provides advanced behavioral analytics designed for growth-driven digital businesses. It enables healthcare organizations to analyze patient journeys, retention, and product usage with advanced segmentation and predictive analytics. Amplitude’s strong privacy controls, data governance and integration options make it suitable for large healthcare enterprises and digital health teams focused on growth and compliance.
Heap
Heap is a digital insights platform that gives teams a complete understanding of customers’ digital journeys to improve conversion, retention, and customer satisfaction. It automatically captures all user interactions and supports HIPAA compliance through BAAs, data encryption, and privacy controls. Its retroactive analytics and journey analysis capabilities allow healthcare teams to gain insights without manual event tagging, reducing implementation complexity. Heap is ideal for healthcare organizations seeking fast deployment and comprehensive analytics while ensuring PHI security.
Freshpaint
Freshpaint is a healthcare-focused platform built with privacy and HIPAA compliance in mind. It can be used to collect website and app data while preventing the sharing of protected health information (PHI) with non-compliant tools, such as analytics or ad platforms. Using cryptographic hashing and anonymous user IDs, Freshpaint enables organizations to analyze complete visitor journeys without exposing individual identities. At the same time, because it serves as an intermediary to prevent PHI from being sent to non-compliant tools, it requires significant technical skills and resources to set up and maintain.
Piwik PRO
Piwik PRO Analytics Suite is a digital analytics and data activation platform that helps businesses collect, analyze, and put user data into action. The platform includes integrated analytics, tag manager, consent management, and customer data platform capabilities, allowing healthcare providers to safely connect first-party data from various touchpoints. It offers compliant data encryption, secure hosting with Microsoft Azure, customizable BAAs, advanced anonymization options, and more. Recently certified as HIPAA-compliant through its SOC-2 Type II audit, Piwik PRO is ideal for healthcare institutions seeking actionable marketing insights without compromising HIPAA compliance.
COMPARISON
The comparison of 9 HIPAA-compliant web analytics platforms
Compare the main features of Piwik PRO, Freshpaint, Matomo, Mixpanel, Amplitude, Heap, Tealium, Adobe CJA and Piano Analytics.
The post The comparison of 9 HIPAA-compliant web analytics platforms appeared first on Piwik PRO.
]]>The post PHI and PII: How they impact HIPAA compliance and your marketing strategy appeared first on Piwik PRO.
]]>Webinar on-demand
A practical guide to digital analytics and advertising under HIPAA
Personally identifiable information (PII) and protected health information (PHI) may seem similar. However, there are critical distinctions between the two. While PII is a catch-all term for any information that can be associated with an individual, PHI applies specifically to HIPAA-covered entities dealing with identifiable patient information.
Keeping HIPAA compliant and protecting patient information requires healthcare organizations to understand the differences between PII and PHI. Especially if they want to use such data to promote their services or improve the digital customer experience.
This blog post explains what differentiates PHI from PII and the key identifiers that change health information into PHI under HIPAA. You will also learn how your organization can protect PHI and run compliant marketing activities.
PHI vs PII
PII Defined
PII stands for personally identifiable information, an American legal term for any information that identifies, links, or relates to a person. The definition of PII can vary depending on the context, such as specific federal or state laws or industry regulations.
Generally, PII refers to:
- Full name
- Home address
- Email address
- Social security number
- Passport number
- Driver’s license number
- Credit card number
- Date of birth
- Telephone number
- Owned properties, e.g., vehicle identification number (VIN)
- Login details
- Processor or device serial number
- Media access control (MAC)
- Internet Protocol (IP) address
- Device IDs
- Cookies
US government agencies and non-governmental organizations often reference PII. Currently, despite ongoing discussions and proposals, there is no comprehensive federal legislation protecting personally identifiable information (PII) in the United States. Various state laws have been enacted to address data privacy, such as those in Delaware, Iowa, Maryland, and Tennessee, which are taking effect in 2025. Also, there are specific federal regulations and laws, like the Protecting Americans’ Data from Foreign Adversaries Act of 2024 (PADFA), that focus on restricting the sale of sensitive data to certain foreign entities.
The National Institute of Standards and Technology (NIST) provides guidelines on the concept of PII, though they are not legally binding unless specifically referenced in a regulation.
Any information about an individual maintained by an agency, including (1) any information that can be used to distinguish or trace an individual’s identity, such as name, social security number, date and place of birth, mother‘s maiden name, or biometric records; and (2) any other information that is linked or linkable to an individual, such as medical, educational, financial, and employment information.
Medical, educational, employment, and financial information all fall under PII. However, the line between PII and other kinds of information is vague. As the US General Services Administration stresses, the “definition of PII is not anchored to any single category of information or technology. Rather, it requires a case-by-case assessment of the specific risk that an individual can be identified”.
What is PHI in healthcare?
Healthcare organizations deal with sensitive information concerning people’s health. In the US, safe parameters for using this kind of data in different contexts, including marketing, are set by the Health Insurance Portability and Accountability Act (HIPAA).
The definition of protected health information is broad. PHI and electronically protected health information (ePHI) mean any identifiable data about the patient, including name, address, date of birth, SSN, device identifiers, email addresses, biometrics, lab or imaging results, medical history, and payment information.
Thus, PHI is a subset of PII that refers explicitly to information processed by HIPAA-covered entities. When health information is combined with a personal identifier, the data becomes PHI.
What are HIPAA-covered entities?
Covered entities are specified in the HIPAA Privacy Rule as health plans, healthcare clearinghouses, and healthcare providers.
The Department of Health and Human Services (HHS) lists the 18 HIPAA identifiers:
- Name
- All geographic subdivisions smaller than a state (street address, city, county, zip code)
- Dates, including birthdate, admission date, discharge date, and date of death
- Telephone number
- Fax number
- Email address
- Social Security number
- Medical record number
- Health plan beneficiary numbers
- Account number
- Certificate/license number
- Vehicle identifiers and serial numbers, including license plate number
- Device identifiers and serial numbers
- Web URL
- IP address
- Biometric identifiers, including fingerprints and voice
- Full face photo
- Any other unique identifying number, characteristic, or code
As a result, not all health information acquired by organizations constitutes PHI. For example, phone numbers and residential addresses alone are not PHI. But if this data is connected with details about a health condition, treatment plan, or other particular health information, it would transform from PII to PHI.
In a Bulletin, the Office for Civil Rights (OCR) at the HHS states that healthcare information collected on a regulated entity’s website or app generally is considered PHI even if:
- The individual doesn’t have an existing relationship with the regulated entity.
- Data such as IP address or geographic location doesn’t include specific treatment or billing information like dates and types of healthcare services.
The original version of the bulletin assumed that anyone visiting a covered healthcare provider’s website was, is, or will be a patient of the provider. The updated bulletin from March 2024 attempted to clarify these provisions. It introduced subjective intent standards for classifying IP addresses as protected health information (PHI). While maintaining that IP addresses combined with health-related webpage visits could constitute PHI, the update added examples distinguishing scenarios like job postings (non-PHI) from cancer care pages (potential PHI) based on inferred user intent.
However, this created operational challenges for hospitals, as determining visitor intent on unauthenticated pages remained impractical. The updated bulletin did not substantively modify HHS’s core position that IP addresses linked to health-related content could trigger HIPAA obligations, despite the ongoing AHA lawsuit.
The HHS provides examples of what parts of a website or app can contain PHI:
- User-authenticated pages will likely contain many forms of PHI, making them subject to HIPAA.
- Some unauthenticated pages include PHI. Whether PHI is being disclosed depends on the visitor’s underlying intentions and whether the page visit relates to the individual’s health care.
- Mobile apps contain PHI provided by the app user and their devices, such as geolocation or device ID.
For more details on what qualifies as PHI, visit the HIPAA journal.
The American Hospital Association (AHA) and co-plaintiffs filed a lawsuit on November 3, 2023, challenging the HHS Office for Civil Rights’ December 2022 bulletin. They argued that the HHS bulletin unlawfully expanded HIPAA’s scope by treating data like IP addresses collected from public-facing hospital websites as PHI, exceeding statutory authority and bypassing proper rulemaking procedures.
In June 2024, a judge ruled in favor of the AHA. The ruling stated that HHS overstepped its authority by expanding the definition of PHI to include IP addresses combined with website visits. On August 29, the OCR decided not to appeal the district court’s decision.
However, it’s crucial to emphasize that the ruling doesn’t vacate other parts of the guidance. The court’s decision was very narrow and only issued in a specific case concerning IP addresses combined with visit data. It doesn’t mean healthcare organizations can downplay HIPAA requirements, freely track users, or ignore HHS’s guidance. Other parts of the bulletin remain in place, like those relating to authenticated pages, such as patient portals.
The issue of protecting PHI in the context of analytical tools hasn’t been settled once and for all. The fundamental issues surrounding the collection and use of PHI by healthcare organizations remain unchanged. While the definitions of PHI and ePHI are well-established, the widespread use and interoperability of modern IT systems make it alarmingly easy for PHI to inadvertently leak into your website or app. Therefore, it’s wiser to stay on the safe side rather than rely on a gray-area interpretation of PHI that maintains the status quo. To protect patient privacy and reduce the risk of hefty fines and loss of trust, organizations must remain vigilant about the data they collect and share with analytics vendors.
The requirements for processing PHI help protect patient privacy and make care coordination easier. The HIPAA Privacy Rule ensures that PHI is shared and used only with patient permission or for care coordination between covered entities. Identifiable health information is not considered PHI unless that organization is a HIPAA-covered entity.
PII and PHI penalties and compliance
Another important area in understanding PII and PHI is the penalties for non-compliance with applicable regulations. As PHI applies specifically to HIPAA-covered entities that possess identifiable health information, using the terms interchangeably can lead to compliance issues. PII and PHI penalties are primarily financial, but in severe cases they may also include incarceration.
PII
To help organizations manage and protect PII appropriately, the National Institute of Standards and Technology (NIST) created the “PII confidentiality impact level” standard, allowing entities to categorize PII into low, moderate, or high-risk levels. The levels are determined by evaluating the potential harm to individuals and the organization if the PII ends up in the wrong hands.
What is high-impact PII for some could be at a low impact level for others. Each organization will have different needs depending on the types of PII they are storing and the way it is organized. For example, Social Security Numbers are more sensitive than phone numbers and may be categorized at a high confidentiality impact level. In addition, a breach involving the information of 30 people will likely be less impactful than one involving 300,000 people.
When a PII breach occurs, businesses must report the incident. US lawmakers have introduced legislation requiring companies to notify the government within 24 hours of a data breach. Many states do not have strict deadlines when businesses report a violation to the government. Data breach notification laws vary state by state. All 50 states, the District of Columbia, Guam, Puerto Rico and the Virgin Islands have laws requiring private businesses, and in most states, governmental entities as well, to notify individuals of security breaches of information involving PII. Check out the list of Security Breach Notification Laws.
Deliberate, unauthorized disclosure of PII to others may result in incarceration and fines of up to $5,000.
PHI
The HIPAA Security Rule strictly regulates PHI breaches. It “establishes national standards to protect individuals’ electronic personal health information created, received, used, or maintained by a covered entity.”
HIPAA penalties are primarily financial and can be applied to healthcare providers, health plans, healthcare clearinghouses, and all other health organizations and business associates who have violated HIPAA rules.
In the case of PHI, HIPAA-covered entities that face a data breach are legally required to notify the HHS and state agencies within 60 days of the breach. If the breach impacts more than 500 residents of a state, organizations must notify major local media outlets through a press release.
In addition, covered entities must send a written notice in the mail to all impacted individuals and post information on the homepage of their website for at least 90 days. Specific requirements vary by state.
The penalties for HIPAA violations are divided into four tiers based on the level of culpability and intent behind the violation. Each level sets out criminal penalties, a fine, and a jail term, if applicable. HIPAA violation fines can be issued up to a maximum of $25,000 per violation category per calendar year. The minimum penalty is $100 per violation.
How to protect PHI in analytics
Health organizations are obligated to protect their patients’ PHI under HIPAA. You must apply a few safeguarding practices while collecting and processing data online.
1. Establish a business associate agreement (BAA) with every platform you use for marketing, advertising, and analytics and every company you’ll share your clients’ PHI with that meets the definition of a “business associate.” If you are a health organization and choose to send PHI to a business associate, you must have a written BAA requiring the associate to comply with HIPAA standards. If you don’t want to create a business associate relationship with the vendor or the vendor will not provide a satisfactory BAA, you cannot disclose PHI to that vendor without individuals’ authorization.
2. Provide breach notification to affected individuals, the Secretary, and the media (when applicable).
3. Address the use of analytics and other data platforms in your risk analysis and risk management processes. They are crucial components of HIPAA compliance, aimed at identifying and mitigating threats to electronic protected health information (ePHI).
4. Implement administrative, physical, and technical safeguards following the HIPAA Security Rule to protect PHI.
Administrative safeguards
Purpose: Focus on policies, procedures, and training to ensure the security of ePHI.
Examples:
- Conducting regular risk analyses to identify potential security threats.
- Implementing policies for workforce training and security management.
- Establishing procedures for emergency situations and incident response.
- Defining roles and responsibilities within the organization related to security.
Physical safeguards
Purpose: Protect the physical environment where ePHI is stored or accessed.
Examples:
- Implementing facility access controls, such as locks and alarm systems.
- Securing workstations and devices that handle ePHI.
- Establishing policies for the proper disposal and reuse of electronic media containing ePHI.
Technical safeguards
Purpose: Implement technologies to secure ePHI from unauthorized access or breaches.
Examples:
- Access controls to ensure only authorized personnel can view or modify ePHI.
- Audit controls to track and monitor access to ePHI.
- Data integrity measures to prevent unauthorized alteration or destruction of ePHI.
- Encryption and secure transmission protocols for ePHI sent over electronic networks.
5. Work with vendors that support values such as privacy by design. Privacy by design is an approach that integrates data privacy considerations into the design of systems, products, and services from the beginning rather than as an afterthought, ensuring data protection is prioritized alongside functionality. Following these values will help you fully control your data and understand what data you collect, store, and transfer.
6. If you can’t sign a BAA with the vendor, de-identify your PHI for research purposes or marketing by removing all 18 HIPAA identifiers. HIPAA-compliant de-identification methods include Expert Determination and Safe Harbor. Once the data is impossible to trace back to one individual, it is no longer PHI and no longer has protection under HIPAA.
It’s important to think through both the legal aspect of data collection in terms of what legal agreements need to be in place with vendors to be in compliance with HIPAA, and the technical aspect of data collection – what data can be stored and where, as well as what data needs to be anonymized prior to storage.
Pat Barry
VP, Data & Analytics at SPM Marketing & Communications
The obligations of healthcare companies that deal with PHI don’t stop there. HIPAA defines five major rules that all organizations that store, record, or share PHI and ePHI must follow. Read them here:
Piwik PRO provides healthcare organizations with fully HIPAA-compliant analytics. Our platform allows you to securely collect and analyze PHI and ePHI and provide better and more personalized patient experiences.
By signing a BAA with us, you can safely send all types of PHI to your analytics setup. If you prefer, you can de-identify all PHI before sending it to our platform. Either way, you can ensure compliance with regulations.
On top of that, we offer the highest privacy and security safeguards to strengthen your data protection. Learn more about HIPAA compliance with Piwik PRO.
HIPAA marketing compliance: Best practices
When exploring HIPAA-compliant marketing strategies, you must first ensure that you disclose PHI only as expressly permitted or required by the HIPAA Privacy Rule. You must obtain explicit written authorization from patients before using their PHI for marketing purposes, which requires a specific, signed consent form. You don’t need authorization to provide essential healthcare services.
Covered entities must have a BAA with the analytics or marketing vendors that they share PHI with. They should also use tools that employ robust security features like user authentication, access controls, audit logs, and end-to-end encryption.
Most analytics platforms, including Google Analytics 4, don’t permit the use of PHI data in their products. These platforms don’t offer BAAs for their standard versions and are not configured to support HIPAA compliance out-of-the-box. It means you must either make an extra effort to avoid passing any trace of PHI to your analytics, or switch to a HIPAA-compliant analytics platform, such as Piwik PRO Analytics Suite.
Read more: Piwik PRO is officially HIPAA-certified!
Remember that data collected from marketing pages and used in retargeting campaigns may constitute PHI. Aside from the 18 types of HIPAA identifiers, including names, addresses, and medical records, user IDs and IPs used for retargeting can easily become PHI. In most cases, using this information for marketing also requires the patient’s authorization and a platform that offers a BAA.
Consider investing in a safe first-party data strategy to use PHI in a way that fully respects HIPAA. Combining data from multiple touchpoints, including your analytics, email marketing software, customer management platforms, and offline sources, opens up many possibilities.
Here are some tips for building a HIPAA-compliant data ecosystem:
- Use HIPAA-compliant customer data platforms (CDPs) to centralize and manage data from various sources, creating accurate and trusted patient profiles and focusing on first-party data.
- Utilize consent management platforms (CMPs) to manage consent forms and ensure data flows align with patient preferences.
- Limit access to authorized personnel only using role-based access controls to prevent unauthorized exposure.
- Implement policies for retaining and deleting PHI in accordance with HIPAA guidelines.
- Adopt policies and procedures for HIPAA compliance beyond technical measures.
- Inform patients about data collection and use, ensuring transparency and trust.
- Clearly communicate the benefits of sharing PHI to enhance patient engagement.
- Regularly monitor data access and changes, maintaining an audit trail to ensure compliance.
I highly recommend using server-side tagging on your website if you’re running digital marketing campaigns that send users to your site. Server-side tagging allows you to scrub PHI/PII from any user data ingested before sending that data back to the vendor.
Pat Barry
VP, Data & Analytics at SPM Marketing & Communications
Learn more about server-side tagging and tracking with Piwik PRO.
There are many different demands for compliant marketing and analytics under HIPAA. Read more:
Final thoughts
Understanding the scope of PII and PHI will help you to maintain HIPAA compliance and protect patient data, especially if you use third-party platforms like analytics. You will also be able to run compliant marketing activities.
To avoid the potential risks of using popular ad platforms or analytics tools in a highly regulated sector such as healthcare, consider employing marketing strategies that revolve around HIPAA-compliant platforms rather than big tech products that put you at risk of breaches and hefty fines. A first-party data strategy can benefit your organization and help you build a relationship with your patients grounded in trust.
If you’d like to learn more about data activation under HIPAA, contact us. We’ll be happy to present some compliant use cases to you.
Unlock better insights and stronger data control in healthcare — see Piwik PRO in action:
Related posts:
- Is Google Analytics HIPAA-compliant?
- Is your analytics project HIPAA-compliant? A complete checklist with 32 questions
- Marketing and advertising in a privacy-first world
- First-party data: The future of digital marketing
- Server-side analytics tracking with first-party collector: What you need to know
The post PHI and PII: How they impact HIPAA compliance and your marketing strategy appeared first on Piwik PRO.
]]>The post How can healthcare organizations benefit from using a customer data platform (CDP) appeared first on Piwik PRO.
]]>The healthcare industry has been slow to embrace digital transformations. Patient data is extremely sensitive, and privacy regulations compel the industry to scrutinize any new marketing or sales strategy. At the same time, regulations like HIPAA require providers to comply with strict standards when managing protected health information (PHI).
Customer data platforms (CDPs) offer a unique opportunity to unify patient data from disparate sources and act on it to improve communication with patients. CDPs allow companies to activate their data to provide integrated experiences across all channels, including appointments, account management, and telehealth.
In this blog post, we will examine how CDPs and data activation can help healthcare organizations integrate and activate their data while remaining privacy-compliant.
What are customer data platforms (CDPs)
CDPs help integrate and manage information about your future and existing patients from multiple sources and points of contact. In healthcare, these can include electronic health records (EHRs), patient portals, mobile applications, social media, and call center interactions.
A CDP offers a unified view of your patients and allows you to use the gathered data to automate processes leading to improved patient acquisition, engagement and retention.
You can use the data to:
- Send timely reminders or follow-ups to patients based on their recent activity.
- Share relevant health information or recommendations matched to patient interests or needs.
- Re-engage patients who started but didn’t finish online forms or bookings.
- Group patients for targeted health campaigns or outreach.
- Notify care teams when patients show signs of needing urgent attention.
Benefits of using a CDP in healthcare
Using a customer data platform (CDP) by HIPAA-covered entities offers several benefits, particularly enhancing patient experiences while ensuring compliance with regulations.
Here are some key advantages of CDPs:
- Data unification: CDPs help unify patient data from various sources, creating a comprehensive view of each patient. Single customer views (SCVs) enhance the ability to provide personalized care and experiences.
- Data silo elimination: By integrating data across different systems, CDPs eliminate data silos, ensuring that all relevant information is accessible and usable for healthcare providers.
- Real-time data management: CDPs often support real-time data management, providing call centers and telehealth agents with up-to-date patient information. With timely insights and responses to patient interactions, call center agents can immediately focus on finding solutions to their issues.
- Integration: CDPs enable seamless integration between various systems and data sources, which improves operational efficiency and provides access to integrated data in one platform.
- Data activation: Healthcare organizations can transform data into actionable insights, improving patient care and decision-making by identifying care gaps, predicting risks, and personalizing treatment plans.
- Enhanced segmentation and targeting: CDPs offer better segmentation and audience targeting by connecting patient data, allowing healthcare providers to tailor services and communications to individual patient needs.
- Improved marketing effectiveness: Use a CDP to unlock healthcare marketing insights to maximize the effectiveness of your campaigns and create personalized experiences.
Customer data platform (CDP) and HIPAA compliance
HIPAA-compliant CDPs provide technical and physical safeguards to protect the PHI they store and process. Such vendors can help them protect patient data with enhanced security features like encryption, safe data storage, access controls, data management, incident response and others.
When looking for a HIPAA-compliant CDP, focus on evaluating the following key areas:
Data security and encryption
Ensure that all patient data is encrypted and hashed immediately upon collection. This includes using protocols like SSL or TLS for data transmission. CDPs also provide identity resolution and data masking to protect patient data.
Compliant hosting
Keep all customer data on a HIPAA-ready public or private cloud with secure backup storage. Private cloud is more optimal due to granular control over the infrastructure and security features.
Minimum necessary principle
HIPAA restricts the scope of collected and disclosed data to what is strictly needed. A CDP should allow granular role-based access controls and data segmentation.
Data retention and deletion
CDPs can automate the implementation of clear policies for retaining and safely disposing of PHI when it is no longer needed.
Auditing and monitoring
Maintain detailed audit logs of data access and modifications for compliance purposes. This will allow you to track who accessed PHI and when, reducing the risk of unauthorized data exposure.
Consent management platforms (CMP)
Many CDPs offer seamless integrations with CMPs. These tools are designed to streamline obtaining, managing, and tracking patient authorization to guarantee all data exchanges contain relevant consents.
Business associate agreement (BAA)
Signing a business associate agreement (BAA) with the CDP vendor allows you to process PHI in a HIPAA-compliant manner. It helps ensure joint compliance and liability for the provided services and establishes clear responsibilities concerning PHI protection.
Patient authorization and HIPAA compliance
Under the HIPAA Privacy Rule, collecting valid patient consent involves specific requirements to ensure the security of protected health information (PHI).
A covered entity must obtain patient authorization before using or disclosing PHI, except for specific exceptions like treatment, payment, and healthcare operations (TPO).
TPO includes, among others:
- Appointment reminders
- Preventive actions
- Individualized recommendations
- Scheduling optimizations
- Telemedicine prompts
- Medication adherence messages
- Basic health campaigns
Another exception to authorization is verbal consent, which is allowed in limited cases, such as hospital directories or notifying family members. Still, disclosures must be minimal, such as name, condition, or location.
If the organization wants to use PHI for purely commercial or marketing purposes unrelated to care, HIPAA requires formal written authorization from patients before their data is used. Such purposes include promoting external or unrelated services, retargeting ads or sharing data with third parties.
You can manage authorization through a HIPAA-compliant consent management platform (CMP) that tracks and enforces consents. A CMP allows healthcare providers to create electronic forms that patients can sign digitally, ensuring a clear and documented authorization record.
Elements of a valid HIPAA authorization
A valid authorization must include the following elements:
- Clear description: The PHI to be disclosed must be clearly defined.
- Patient identification: The patient’s printed name must be included.
- Recipient details: The individuals or entities authorized to use or disclose the PHI must be specified.
- Purpose of disclosure: The purpose of the use or disclosure must be detailed.
- Expiration date: The authorization must include a date after which it is no longer valid.
- Patient signature: The patient must sign the authorization, and a copy must be provided to them.
Patients can revoke their authorization in writing at any time, and covered entities must respect this revocation.
Data de-identification
HIPAA names two valid de-identification methods: Safe Harbor and Expert Determination.
De-identified data can be used for statistical analyses, predictive modeling, or marketing that doesn’t require identifying specific patients. Once PHI is de-identified, the restrictions of the HIPAA Privacy Rule no longer apply because the data contains no individually identifiable health information.
HIPAA also allows using a limited data set under a data use agreement. A limited data set contains identifiable healthcare information that HIPAA-covered entities can share with certain parties for research purposes, public health activities, and healthcare operations without prior authorization from patients. However, if you want to take advantage of this method, ensure you meet the conditions specified by the HIPAA Privacy Rule.
Learn more about HIPAA compliance in marketing and analytics:
Data activation use cases in healthcare
CDPs can help improve patients’ exposure to providers, including onboarding, finding care, and post-care adherence.
You can create audiences of users matching specific demographic or behavioral conditions, such as their preferences, browsing or treatment history, symptoms, subscription, and more. Then, you can activate the audience by providing them with easy access to relevant information and services. Your activations can include showing on-site banners and sending emails or SMS, push notifications, in-app messages, and more.
You can combine data activation with other platforms, such as tag management systems. You’re also able to enrich data in a CDP with information imported from different sources, like ad platforms or CRMs.
Here are some suggestions for data activation use cases in healthcare:
Personalized treatment plans
- Create audiences of users based on their individual health records, browsing and purchase history, and contact preferences.
- Activate the audience by generating tailored treatment recommendations or medication plans and sharing them with patients via secure portals or apps.
Real-time appointment optimization
- Create audiences of users based on their patient preferences and provider availability. You should integrate the CDP with appointment scheduling systems to make this possible.
- Activate the audience by automating scheduling and sending pre-appointment reminders to reduce no-shows.
Enhanced telemedicine experiences
- Create audiences of new patients before their first appointment or a specific type of test.
- Activate the audience by encouraging them to use self-service tools and provide details of their conditions and preferences before their appointment. With this information, clinicians will have access to patient details that will allow them to personalize telemedicine consultations.
- After the appointment, you can request the audience to leave feedback, which you can use to improve future telehealth sessions.
Medication adherence monitoring
- Create audiences of users based on the available prescription data and patient adherence.
- Activate the audience by sending automated refill reminders or alerts for missed doses.
- You can also provide pharmacists and doctors with adherence reports for follow-ups.
Population health management
- Create audiences using aggregated data from diverse populations based on demographic data and identify care gaps and high-risk groups.
- Activate the audience by implementing targeted interventions for underserved communities, such as preventive care campaigns for different age groups.
Acquiring new patients
- Create audiences of users who haven’t used your services before but have been browsing pages about them.
- Activate the audience by showing on-site banners in real-time to encourage them to learn more about your offer, book an appointment, or test.
Cross-promotion campaigns
- Create audiences of users based on their current usage of your services, such as treatment history, health conditions, or subscription plan.
- Activate the audience by recommending related services they might be interested in or higher treatment plans for frequent users.
Let’s go through two step-by-step examples of data activation using Piwik PRO CDP:
Preventive care
1. In Piwik PRO CDP:
- Create an audience based on user/patient attributes indicating they may be at risk of chronic diseases like diabetes or heart disease, as well as web behavioral data like interaction frequency and recency.
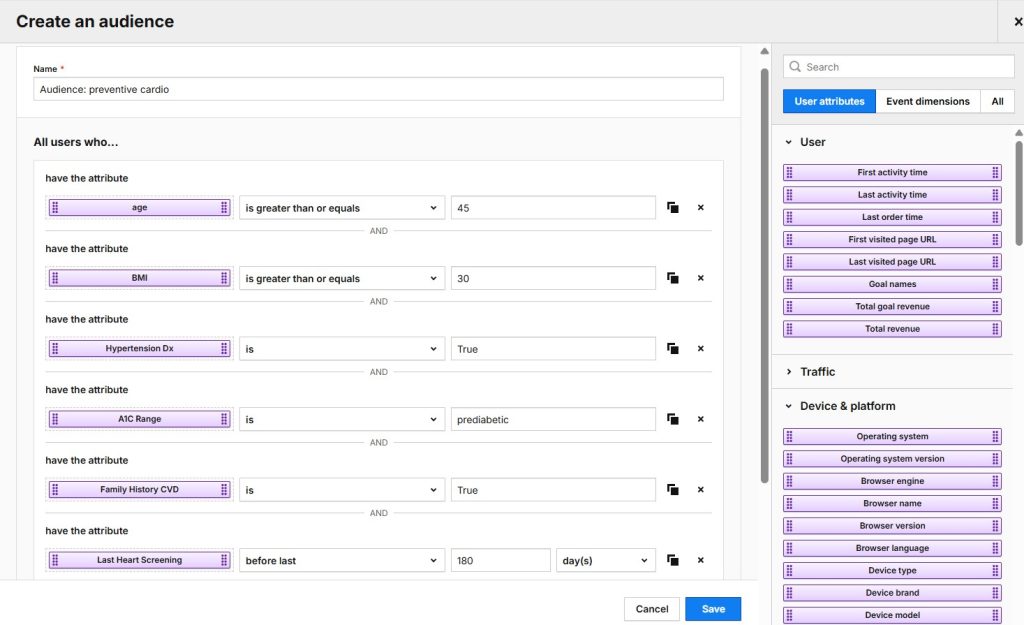
2. In Tag Manager:
- Add a custom tag or content tag with banner styling and text content.
- Add an audience detection trigger.
3. Activate the audience in the CDP by showing an on-site banner with personalized care instructions or recommendations for taking preventive measures.
Patient engagement campaigns
1. In Google Ads:
- Run a campaign promoting cardiovascular disease screenings covered by Medicare Part B.
- Drive users to a landing page with educational content and screening eligibility details.
Note: Such screenings are often covered under government or government-sponsored programs (such as Medicare Part B every 5 years). According to HHS guidance, this type of communication is not considered marketing under HIPAA.
2. In Piwik PRO CDP:
- Create an audience of users who came from the Google Ads campaign and have shown high interest via their web behavior.
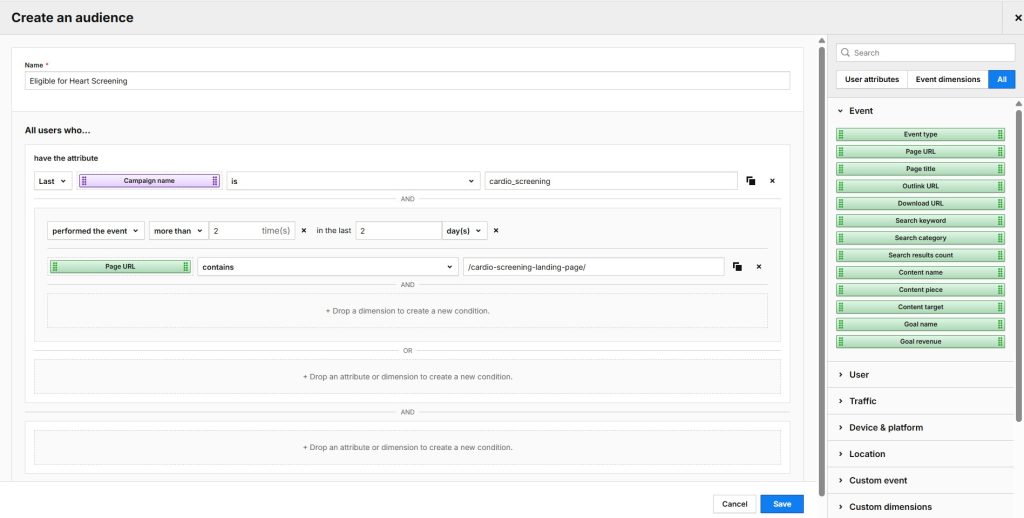
3. Activate the audience in the CDP via a webhook or API by sending the attribute indicating the user’s interest in cardiovascular screening to an appointment portal like Phreesia. You must sign a BAA with the platform.
4. In the appointment portal:
- Check if the user already has an appointment.
You can skip this check if you’re feeding data into the CDP from the appointment portal and include a ‘no-appointment-yet’ condition in Step 2.
- If not, send the following text message to the user: “You may be eligible for a free heart screening. View your secure invitation here”.
Piwik PRO and HIPAA compliance
If you want to start activating your data, choose a HIPAA-compliant platform that will let you do it safely yet effectively.
Piwik PRO offers an integrated platform consisting of analytics, tag management, consent management, and a customer data platform.
With an intuitive UI, easy-to-use, customizable reports and dashboards, and seamless integrations with other tools, you can adjust data processes to your needs. Throughout this, we offer personalized support, onboarding and training.
On top of functionality, you can count on a range of features to support your organization in complying with HIPAA. These include:
- Compliant hosting: Piwik PRO offers hosting on HIPAA-compliant Microsoft Azure data centers based in the US, allowing organizations to know how and where their data is being stored.
- Business associate agreement (BAA): Piwik PRO offers a customizable BAA, helping clients ensure sensitive health information is handled following HIPAA standards. If you prefer, you still have the option to de-identify all PHI before sending it to our platform. Either way, you can ensure compliance with HIPAA.
- Encryption: Data is encrypted at rest and in transit using secure protocols like 256-bit AES encryption, ensuring that sensitive health information remains safe.
- Advanced user permissions: Piwik PRO provides granular access controls, allowing organizations to restrict access to sensitive data to authorized personnel only.
- No sharing of ePHI: Piwik PRO does not share electronic protected health information (ePHI) with third parties or reuse it for other purposes, maintaining data privacy.
- Regular security audits: The platform undergoes regular privacy and security audits by external bodies to ensure high-security standards.
- ISO 27001 and SOC 2 Type II certifications: Holding these certifications, including a HIPAA compliance assessment, demonstrates Piwik PRO’s commitment to robust security and compliance standards.
Read more about Piwik PRO and HIPAA compliance.
Final thoughts
Patients expect personalized interactions with their providers, but achieving this on a large scale is challenging. Using customer data platforms (CDPs) in healthcare is a way to provide better experiences at every stage of the patient journey. User expectations are ever-changing, and organizations that are willing to adapt can better meet their needs. Healthcare is personal, and with a strategic application of CDPs and data activation, healthcare organizations can deliver the right message when it matters most.
Reach out to us and learn how your healthcare organization can benefit from data activation with Piwik PRO:
The post How can healthcare organizations benefit from using a customer data platform (CDP) appeared first on Piwik PRO.
]]>The post HIPAA, marketing and advertising: How to run compliant campaigns in healthcare appeared first on Piwik PRO.
]]>Webinar on-demand
A practical guide to digital analytics and advertising under HIPAA
Disclaimer: This blog post is not legal advice. Piwik PRO provides privacy-friendly analytics software, but doesn’t provide legal consultancy. If you’d like to make sure that you comply with HIPAA guidelines, we encourage you to consult an attorney.
Healthcare organizations deal with tons of sensitive information concerning people’s health. It needs to be handled with proper care. In the US, safe parameters for using this kind of data in different contexts, including marketing, are set by the Health Insurance Portability and Accountability Act (HIPAA).
Unfortunately, many companies are still unaware of the provisions of the law and the potential consequences of breaching its rules. The recent scandal around the use of Facebook pixels inside the patient portals of renowned medical institutions is sad proof of that.
In this article, we explain which marketing practices are unlawful under HIPAA and why. We also present some practical measures you could take to make your retargeting campaigns HIPAA-compliant.
Finally, we provide you with more privacy-friendly alternatives to retargeting that can help you do effective marketing and engagement campaigns without violating patients’ privacy.
Healthcare providers continue to misuse patient data
The recent lawsuit filed against the UCSF Medical Center and the Dignity Health Medical Foundation has caused a stir in the world of healthcare. According to the lawsuit, the healthcare providers collected sensitive health information from patient portals and used it for retargeting ads on Facebook, transmitting the data to Facebook without patient consent.
Healthcare data breaches, although alarming, are neither new nor rare. As of July 2023, healthcare organizations reported 330 breaches of sensitive health information affecting 41.4 million individuals to the HHS Office for Civil Rights, compared to 52 million affected in all of 2022. Many breaches involve cyberattacks and ransom demands, but some involve the inadvertent disclosure of private health data through tracking technologies, known as pixels, utilized by social media companies. Last year, The Markup found that 33 of the top 100 US hospitals used Facebook pixels on their websites. Seven of them used tracking codes on patients’ portals behind login walls.
New guidance on using tracking technologies
Many healthcare companies remain unaware of HIPAA provisions and ways to comply with them. One of the factors affecting the increased number of HIPAA breaches is HHS’s bulletin from December 2022 that provides strict guidance on the use of third-party cookies, pixels and other tracking technologies by healthcare companies. This bulletin did not change HIPAA law itself, but rather provided an interpretation from HHS of how existing HIPAA rules apply to these technologies. This interpretation broadened what the HHS considers to be protected health information (PHI), which has sparked many controversies.
Earlier in 2023, numerous healthcare organizations submitted breach reports, acknowledging they had violated the December guidance from HHS. Telehealth provider Cerebral filed a data breach notification with HHS, admitting to having disclosed PII to other parties without sufficient HIPAA-protective measures. In July 2023, the FTC and HHS sent a joint letter to approximately 130 hospital systems and telehealth providers to alert them to the risks of tracking technologies on sites and apps that can impermissibly disclose consumers’ sensitive personal health data to third parties.
The AHA lawsuit against the HHS bulletin
The American Hospital Association (AHA) filed a lawsuit against the US Department of Health and Human Services (HHS) Office for Civil Rights (OCR) in November 2023, challenging its guidance on the use of online tracking technologies. This lawsuit, joined by several hospital associations and health systems, aimed to block the enforcement of OCR’s December 2022 bulletin, which expanded the definition of PHI to cover metadata such as IP addresses combined with webpage visits collected through tracking tools like pixels on hospital websites and apps.
In June 2024, a judge ruled in favor of the AHA, declaring that the OCR had exceeded its statutory authority under HIPAA. It is crucial to understand the narrow scope of this ruling. The court specifically addressed the use of IP addresses and website visit data from unauthenticated web pages. The ruling does not invalidate other parts of the HHS guidance, particularly those relating to authenticated pages or the use of other types of data. The fundamental responsibility of healthcare organizations to protect PHI remains unchanged. Practices allowed under HIPAA concerning the use of tracking technologies like analytics platforms are still subject to interpretation. Consequently, healthcare providers should err on the side of caution and choose an approach to analytics that will ensure security and compliance.
What happens if you don’t comply with HIPAA
The unauthorized use of protected health data for marketing and advertising may have some serious consequences. HIPAA breaches lead to the harshest and most direct penalties, including fines of up to $1,806,757, and in some cases, even criminal sanctions.
Malpractice concerning healthcare data can also damage patients’ trust and affect their relationship with their healthcare provider. As a recent study shows, patients who worry about their electronic health records being compromised in a breach are three times more likely to withhold information from their physicians.
Marketing and HIPAA: The problem goes beyond Facebook
Under HIPAA, marketing is defined as “a communication about a product or service that encourages recipients of the communication to purchase or use the product or service”. An example of marketing includes sending promotional emails about new medical devices or services that encourage purchases.
HIPAA generally requires covered entities to obtain written authorization from individuals before using or disclosing protected health information (PHI) for marketing purposes. The increased costs and complexity in obtaining these authorizations can hinder targeted marketing efforts.
It’s worth noting that communications related to treatment, case management, care coordination, or recommendations for alternative therapies are not considered marketing and don’t require patient authorization.
Examples include:
- Prescription refill reminders.
- Information about health-related services included in a health plan.
- Communications aimed at improving patient care without promoting specific products.
It’s vital for healthcare organizations to clearly differentiate between permissible healthcare-related communications and those classified as marketing. They must also ensure that any tools or methods used for marketing (like email campaigns) are HIPAA-compliant.
To assess if your marketing use case requires patient authorization, read the guide on marketing by the US Department of Health and Human Services (HHS).
To learn about the elements of compliant patient authorization, look into the resources provided by the HHS.
The issue of defining PHI
Marketers must stay updated on what constitutes PHI in the digital age to avoid using data that could be considered protected without proper authorization.
PHI includes any individually identifiable health information, which is a category that can be interpreted broadly. This means that even seemingly innocuous data, such as IP addresses or contact information, could be considered PHI if linked to health-related information.
HIPAA’s definition of protected health information lists 18 types of data, including names, addresses, and medical records, but also user IDs and IPs often used to recognize visitors across channels. Even data collected from marketing pages and used in retargeting campaigns may constitute PHI.
Some publishers, such as Facebook, serve ads on social platforms available after logging in. Data that doesn’t include health information may become PHI when combined with user data from social networks.
Consider employing data aggregation or anonymization to remove individual identifiers, which makes it no longer PHI. Another method involves using a limited data set that can be used for marketing purposes with a data use agreement.
Signing a BAA
BAAs are essential tools for ensuring HIPAA compliance and protecting sensitive patient information when covered entities work with third-party vendors. By signing a BAA with a marketing or advertising vendor, a HIPAA-covered entity can securely share PHI with them.
Popular advertising platforms, including Facebook, Google, and LinkedIn Ads, don’t give you the option to sign a business associate agreement (BAA). The same issue applies to many other products used by marketers, like analytics. Most of the platforms available on the market, including Google Analytics 4 and Adobe Analytics, don’t offer BAAs and forbid the use of PHI data in their products.
These platforms cannot be configured in a HIPAA-compliant manner without significant customization, such as the lengthy and complex process of de-identifying PHI. A covered entity can’t just use GA4 or Adobe Analytics and expect to be compliant. The most future-proof approach involves switching to a marketing or analytics provider that will sign a BAA and help you process patient data with the proper safeguards.
All these factors limit the ways you can do marketing in healthcare, especially when it comes to retargeting and other practices relying on user identifiers. That said, running retargeting campaigns is not impossible under HIPAA.
How to run compliant ad campaigns under HIPAA
Using retargeting in healthcare is possible but requires some serious precautions.
Here are some tips for HIPAA-compliant advertising:
- Remove marketing pixels from your password-protected apps and websites, such as patient portals. Consider limiting their use to your homepage. Some subpages of your website, such as blog posts about a specific disease or treatment, may still contain health information and can pass it to advertising platforms.
- Strip your data of any traces of PHI before you push it to ad networks. Make sure to get rid of any unique identifiers and pieces of data that would allow an individual to be identified. Follow the privacy guidelines of your chosen ad platform.
- Create remarketing campaigns based on simple and broad targeting, for example, website visits. This way, instead of targeting individuals, you create broad remarketing campaigns that don’t involve PHI.
- Consider using a safe tag management system for better control over the information you send to the ad platforms. This way, you will control where and when pixels are allowed to run.
These campaigns will be less effective than traditional remarketing, since stripping your data from user identifiers removes the layer of personalization. However, they are still a good choice if you want to continue using ad platforms in your marketing.
That said, the compliance of your retargeting ads will depend on the type of healthcare business you’re in. The narrower and more sensitive the subject is, the greater the risk of disclosing PHI to a publisher.
Let’s consider three scenarios:
- You want to prepare a remarketing campaign for a health insurance provider. Hence, you create a general campaign that targets users who have visited your website and presents them with non-personalized ads that promote your offer. In this case, you don’t rely on PHI, and the message of your ad doesn’t contain information about the visitor’s condition or health issues. Given that you’ve gotten rid of all potential user identifiers, your advertisement is most probably HIPAA-compliant.
- You’re running a fertility clinic and plan to create a retargeting campaign based solely on page visits without using demographic data. Unfortunately, displaying ads related to sensitive issues, such as infertility, might still violate user privacy and bring compliance risks. By using data about a visit on a highly specialized website, you disclose information about a person’s potential health issues and share it with an ad platform.
- You’re in charge of digital marketing for a dermatological clinic. A person has visited your website in search of dermatitis treatment. Retargeting them with an ad promoting a treatment for the skin condition they looked up would violate the patient’s privacy. But an ad that promotes your clinic without mentioning any particular health issues should be a safe choice.
Keep in mind that these are only general guidelines and examples. Each ad campaign must be carefully assessed to ensure that it does not directly or indirectly reveal protected health information.
Consider implementing search engine advertising (SEA) or contextual advertising, which do not rely on PHI or sensitive patient data but instead use keywords.
You can also integrate data from your ad platforms with a secure analytics platform, such as Piwik PRO Analytics Suite. This will allow you to evaluate the performance of your ads without sending this data back to Google or Facebook and adjust your campaigns accordingly.
How to run compliant marketing campaigns under HIPAA
HIPAA-covered entities can engage in compliant marketing by following these strategies:
Content marketing
- Create educational content that does not require PHI, such as blog posts on health topics, videos about common medical conditions, and infographics on preventive care.
- Focus on general health information rather than specific patient cases.
Social media engagement
- Use social media to share general health tips and wellness advice, avoiding discussions of specific patient cases.
- Implement disclaimers to clarify that direct medical advice is not provided on social platforms.
- Educate staff on HIPAA-compliant social media practices.
Email marketing
- Obtain proper consent for marketing emails and use secure, HIPAA-compliant email platforms.
- Focus on general health information and practice updates rather than personalized health data.
Onsite retargeting and personalization
- Reengage patients directly on your website or inside your app and serve them special offers, discounts, or recommendations.
- Get upsell and cross-sell opportunities, which may often not require patient authorization.
Creating a first-party data marketing strategy
Despite your best efforts, marketing campaigns run on popular advertising platforms always pose some compliance risks. These platforms weren’t built for such privacy-sensitive industries as healthcare.
For greater peace of mind, consider investing in a safe first-party data ecosystem to use the potential of PHI in a way that fully respects HIPAA.
The benefits of a first-party data marketing strategy include:
- Better compliance – Operating on first-party data helps you comply with data protection laws such as HIPAA. First-party data stays in the hands of those who collect it, and that gives more control and transparency over what happens with the data.
- Data accuracy – First-party data is more accurate because you obtain it directly from your patients, unlike third-party data that is often aggregated from various data sets. Also, this data comes from your audience, making it more relevant to your business.
- Patient trust – As you gather data first-hand from users and inform them about all processing purposes, you build trust and solid relationships with them.
- Enhanced personalization and segmentation – First-party data enables targeting content recommendations and messages at a more granular level. Relying on PHI in a safe data ecosystem will allow you to create detailed segments of users based on characteristics such as demographics or subscribed health plans. This wouldn’t be possible or permitted with third-party data.
- Increased customer engagement – The direct relationships built with site visitors and previous customers create many opportunities for customer experience optimization. As you gather data on customer engagement with the site and different digital assets, you gain key insights into what it needs to do better.
Customer data platforms (CDPs) and HIPAA compliance
You can use a customer data platform (CDP) to establish and manage a first-party data strategy. CDPs are not HIPAA-compliant by default, so you must carefully choose the right tool.
When evaluating a CDP for HIPAA compliance, look for the following security features:
- Data encryption at rest and in transit.
- Role-based access controls to limit PHI access.
- Audit logs for tracking PHI access and modifications.
- Consent management to track patient consent for marketing communications.
- Vulnerability scanning and conducting penetration tests.
- Incident response plan for data breaches.
- Physical security measures.
A HIPAA-compliant CDP lets organizations combine data from multiple touchpoints, including your analytics, email marketing software, customer management platforms, consent managers, offline sources, and more.
This helps companies connect siloed data to create unified patient records and opens up many possibilities for effective marketing activities to improve users’ digital experiences. CDPs can store consent centrally and use it to ensure compliance across all connected downstream systems.
One of the key features of a CDP is data activation, which allows you to target users with relevant content or recommendations.
Here are some ideas for activations that healthcare organizations can employ:
- Creating tailored treatment or medication plans and sharing them with patients via secure portals or apps.
- Showing real-time on-site banners to encourage users to learn more about your services.
- Sending emails reminding users to finish booking a test or a doctor’s visit.
- Providing recommendations for higher treatment plans for frequent users.
How to find a HIPAA-compliant marketing vendor
What makes a MarTech vendor the right partner for a HIPAA-covered organization? As mentioned, a willingness to sign a business associate agreement (BAA) is essential.
A BAA is a contract between a HIPAA-covered organization and its business associates. It obliges both sides of the contract to protect PHI and comply with the guidelines provided by HIPAA. This means ensuring the proper standards of data encryption, private hosting, data minimization options, and other safety measures required by the act.
Keep in mind that signing a BAA is not a universal solution – evaluate the marketing platform’s agreement, terms of service, and data management processes diligently.
There are also additional security features that you can look for in your chosen marketing tools, such as:
- User authentication methods to ensure unique login credentials to access the platform for each authorized employee. For increased security, the platform should enable two-factor authentication (2FA).
- Access controls limit access to sensitive data and should be set based on an employee’s job function. Not all employees should have full access to the platform – they should only be granted access to the data that they need to perform their job.
- Audit logs help ensure that data is only accessed when it should be. Audit logs can be used to determine access patterns for each employee, enabling administrators to identify when an employee is accessing data excessively. This can help quickly detect breaches.
- End-to-end encryption enabled when electronic PHI is created, stored, transmitted, or received using a software platform.
- Storage of PHI on an encrypted offsite data backup server.
Piwik PRO gives you the option to sign a BAA, on top of many other HIPAA-protective measures, such as:
- Secure hosting in HIPAA-compliant data centers.
- Safe backup storage with maximum recovery capability.
- Data encryption and transmission mechanisms.
- Audit log and change log.
- Full data control, and more.
Read more about how Piwik PRO approaches HIPAA compliance.
If the vendor you choose won’t sign a BAA with you, you need to de-identify all data that can be considered PHI before sharing it with the vendor. Such data is deprived of any identifiers, so it is no longer viewed as PHI, removing it from the scope of HIPAA. At the same time, de-identified data lacks a lot of valuable information that would make your marketing campaigns more effective.
Alternatively, find a MarTech platform that offers on-premises hosting. If the vendor doesn’t have access to your infrastructure, they won’t be considered your business associate, so you won’t have to sign a BAA with them. However, maintaining such infrastructure requires extensive resources and time, so not every company will be able to use this option. You can also look into other secure, less resource-heavy options developed over the years, such as a private cloud.
Check out our review of HIPAA-compliant analytics platforms to choose the right analytics provider for your organization.
Marketing and HIPAA: A summary
Using popular ad platforms or non-compliant marketing platforms in a highly regulated sector such as healthcare puts organizations at risk of data breaches and issues with regulatory compliance. Consider employing alternative marketing strategies that don’t involve products from Big Tech.
A first-party data strategy can bring many benefits to your organization and help you build a trust-based relationship with your patients. Opt for HIPAA-compliant marketing and analytics platforms that employ the highest security safeguards and offer business associate agreements (BAAs).
If you want to learn more about how Piwik PRO can support you in providing better patient experiences while maintaining HIPAA compliance, reach out to us:
The post HIPAA, marketing and advertising: How to run compliant campaigns in healthcare appeared first on Piwik PRO.
]]>The post Is Google Analytics HIPAA-compliant? appeared first on Piwik PRO.
]]>Webinar on-demand
A practical guide to digital analytics and advertising under HIPAA
SUMMARY
- Google Analytics isn’t HIPAA compliant for covered entities handling Protected Health Information (PHI). Google doesn’t offer a Business Associate Agreement (BAA), which is crucial for HIPAA compliance when using a third-party analytics platform.
- Using Google Analytics while collecting PHI/ePHI puts healthcare organizations at risk of violating HIPAA regulations. Google may store data in various locations and use it for advertising or improving their services, which conflicts with HIPAA’s requirements.
- Healthcare organizations must ensure that no traces of PHI are sent to Google Analytics, which can be challenging due to the potential for accidental disclosures. For full HIPAA compliance, healthcare organizations should consider using analytics platforms that offer a BAA and provide specific safeguards.
- Vendors like Piwik PRO, Mixpanel, Heap, Amplitude, and Freshpaint will sign a BAA, with Piwik PRO offering comprehensive analytics and data activation capabilities along with HIPAA-specific compliance features.
Healthcare organizations use analytics platforms to collect and analyze data about their patients. The data helps them improve the quality of digital services and personalize content and advertising. It also contributes to reducing data administration costs.
Using analytics tools in a strictly regulated sector such as healthcare requires caution, especially if you operate in the US or work with US patients. In this case, you must process and store protected health information (PHI) in compliance with the Health Insurance Portability and Accountability Act (HIPAA).
Healthcare entities cannot engage in the impermissible disclosure of PHI to tracking technology vendors. This is particularly important now with the expansion of sensitive information collected by vendors like Google Analytics. Disclosing PHI in a manner consistent with HIPAA has become more critical than ever.
In addition, patients are increasingly aware of their legal rights and data security. A focus on HIPAA compliance helps maintain patients’ trust.
What is HIPAA?
HIPAA is a federal law that sets standards for processing, storing and disclosing sensitive protected health information. It applies to all forms of protected health information – electronic, written or spoken.
If you want to know more about HIPAA requirements for professionals, check the website of the US Department of Health & Human Services.
Healthcare analytics – Google Analytics and HIPAA
If you use Google Analytics or similar software, you’re likely already optimizing your website to serve your customers better. But what about Google Analytics and HIPAA compliance?
In short – if you’re a HIPAA-covered entity, using GA4 puts you at serious risk of a HIPAA breach.
Using Google Analytics to collect and process PHI and ePHI
In this scenario, you want to use analytics data and protected health information (PHI and ePHI).
PHI refers to any information relating to a patient´s condition, the past, present, or future provision of healthcare, such as lab or imaging results and medical history, or payment for such services. When identifiers are included in the same record set, PHI becomes individually identifiable health information and is thus protected when it is transmitted or maintained in any form by a covered entity.
Not all health information gathered by healthcare organizations is considered PHI. For example, in most cases, phone numbers, email addresses, or social security numbers alone are not PHI. However, if this data is connected to details about a health condition, treatment plan, or other particular health information, it would transform from PII into PHI.
Meanwhile, using GA4 to track PHI is far from being HIPAA-compliant.
Take a look at the HIPAA disclaimer from Google’s website:
HIPAA disclaimer
Unless otherwise specified in writing by Google, Google does not intend uses of Google Analytics to create obligations under the Health Insurance Portability and Accountability Act, as amended, (“HIPAA”), and makes no representations that Google Analytics satisfies HIPAA requirements. If you are (or become) a Covered Entity or Business Associate under HIPAA, you may not use Google Analytics for any purpose or in any manner involving Protected Health Information unless you have received prior written consent to such use from Google.
Google states that Google Analytics doesn’t satisfy HIPAA requirements. And you can’t use Google Analytics for any purpose involving PHI if you are:
- A covered entity – hospital, clinics, insurance company, healthcare clearinghouse, etc.
- A business associate – for example, an external company hired to perform legal services, data aggregation, management or data analysis.
Moreover, if you want to use a tracking technology (such as an analytics platform) that collects and processes PHI, you must sign a business associate agreement (BAA) with the vendor. Google does not offer this option.
Why Google won’t sign a BAA with you
There are two possible reasons why Google won’t sign a BAA with organizations covered by HIPAA:
- Google doesn’t offer on-premises hosting and data residency of your choice. It means that all data tracked by the platform will be stored in randomly assigned data centers within and outside the US. This breaks the HIPAA accountability rule – you don’t know your patients’ exact data location.
- Google’s terms and conditions describe how it uses tracked data. Google uses the data to develop new services, measure the effectiveness of advertising, and personalize content and ads. Using any PHI or ePHI in an advertising context might be a serious violation of HIPAA.
As a result, if you pass any trace of PHI/ePHI into Google Analytics, you’rebreaking HIPAA regulations and Google’s terms of service. This may result in the termination of your GA account.
Many ways in which third-party tracking technologies, like Google Analytics, collect and track user information are not apparent to users visiting your website or app. These technologies send information directly to the third parties that develop them. Users’ unique identifiers and other collected information allow Google Analytics to create individual profiles for each user. They may continue to track users and gather information about them even after they navigate away from the original website to other websites. Such practices are particularly serious when they concern sensitive information like healthcare data.
Also, consider this case from your patients’ perspective. Your visitors trust your website and search for information about their illnesses, including cancer or depression. If they later see ads related to that illness on an unrelated page, you’ll be in trouble. This not only violates HIPAA provisions but also leads to the loss of patients’ trust in your organization.
Using Google Analytics without collecting and processing ePHI or PHI
If you use Google Analytics as a healthcare organization without collecting and processing PHI/ePHI, you might comply with HIPAA. However, this requires additional work and precaution from your side. You need to ensure you don’t send any traces of PHI/ePHI to Google Analytics – mistakes can be damaging to your company’s reputation and result in HIPAA breaches. This is also the case if you violate HIPAA rules unknowingly.
According to the OCR’s Bulletin, PHI can be found on different parts of your website, such as post-login areas, which will likely contain lots of PHI, but also on unauthenticated pages or mobile apps. For example, PHI disclosures can occur if a patient’s use of the page or app is related to a health condition (for example, they are using appointment scheduling pages and symptom-checker tools, or they are looking for specific treatment options) and is coupled with PII (for example, name, email address or IP address).
Whether PHI is being disclosed depends on whether the page visit relates to the individual’s health care or what the visitor’s underlying intentions are – and that’s difficult to determine with complete certainty.
Note: In June 2024, a judge ruled in favor of the AHA, declaring that OCR had overstepped its authority when issuing its guidance. On August 29, the OCR decided not to appeal the district court’s decision.
The court ruling and HHS’ decision not to appeal it do not mean that the issue of protecting PHI in the context of analytical tools has been settled once and for all. The ruling was issued in a specific case, indicating that an IP address combined with visit data from an unauthenticated web page does not constitute PHI. However, the ruling does not vacate other parts of the guidance, like those relating to authenticated pages such as patient portals. While the court’s verdict may serve as a benchmark for later decisions on possible HIPAA violations, the complexity of PHI protection and the multiplicity of contexts involved would dictate special caution.
The fundamental issues surrounding healthcare organizations’ collection and use of PHI remain unchanged. Therefore, it’s wiser to stay safe rather than rely on a gray-area interpretation of PHI that maintains the status quo. Organizations must remain vigilant about the data they collect and share with analytics vendors in order to protect patient privacy and reduce the risk of hefty fines and loss of trust.
GA4 and client-side vs. server-side Google Tag Manager (GTM)
There is a difference between using client-side and server-side GTM when it comes to HIPAA compliance.
When using client-side GTM, the user’s browser communicates directly with third parties, making it challenging to control the information bring shared. Depending on how your website or app processes user information, there might be a risk of sharing PHI in HTTP requests. Consequently, this option is far from compliant with HIPAA.
Server-side GTM, when correctly set up, helps you control what data you share with Google. User data is only sent to the server hosting the GTM container rather than being shared with multiple third-party servers. You can remove any PII within the server container before passing the data on to marketing partners. However, consider two things:
- GTM’s use policy also requires compliance with Google Analytics’s terms of service, which state that you can’t send PII to GA4 – and PHI is a subset of PII.
- You must adequately de-identify any data matching the definition of PHI before sending it to Google, which is a lengthy and error-prone process.
Read more about using server-side GTM and GA4 as a HIPAA-covered entity.
Considering all these aspects, using Google Analytics by HIPAA-covered entities is very risky. If you want to take that risk, you must ensure no PHI finds its way into the platform.
Take a look at these sample URLs:
https://healthclinics.com/your_account_john_hill/stomatologist_nelson_greenhttps://healthclinics.com/url8554
The first URL contains PHI – your patient’s name and their doctor’s name and specialization. Meanwhile, the second URL is scrubbed of PHI and shows only a universally unique identifier. Ensure your settings and site architecture are properly configured so the first URL switches to the second one before it reaches your analytics.
One way is to de-identify data so it is no longer considered PHI and does not fall under HIPAA. However, de-identification is a complex and time-consuming process that requires strict organizational measures. It’s especially difficult for certain types of data, such as custom dimensions or event attributes.
The rules under HIPAA concerning the use of tracking technologies like analytics platforms continue to be subject to interpretation. While the definitions of PHI and ePHI are well-established, the broad adoption and connectivity of modern technologies increase the risk of PHI accidentally leaking into your website or app.
De-identified data may be less valuable for those who analyze it. Because it’s stripped of identifiers, you can’t use it to personalize content for returning visitors – they always appear as new visitors. You also can’t analyze patients’ journeys and create detailed conversion attribution.
Issues with user privacy and data security are not the only limitations of Google Analytics 4 (GA4). The platform continues to offer significant conversion tracking discrepancies, inaccurate traffic reports, problems with the Google Ads integration, and other issues that can lead to confusion and misinterpretation of marketing performance metrics.
Learn more: Google Analytics 4 (GA4) problems: The state of GA4 4 months after UA sunset
How to make your analytics HIPAA-compliant
Switching to an analytics platform that allows you to process patient data with the proper safeguards can help you avoid the risks and limitations of using GA4.
The best way to support your HIPAA compliance efforts is to find an analytics vendor that will sign a business associate agreement (BAA). This will allow you to share PHI/ePHI without de-identifying or restricting its flow to the platform.
Here are a few analytics vendors that offer a BAA:
- Piwik PRO
- Mixpanel
- Heap
- Amplitude
- Freshpaint
- Adobe* (Applies to Adobe Customer Journey Analytics. You can’t sign a BAA to use Adobe Analytics.)
Some platforms offer on-premises hosting, which means you don’t share data with third parties and thus don’t need to sign a BAA. However, this option makes you responsible for your data infrastructure’s security, so ensure you have the resources and expertise to maintain it. You can self-host your analytics with Piwik PRO by storing your data in a dedicated database.
When selecting the right tool, review each platform’s strengths individually and look in detail at your specific needs in terms of functionality, ease of use, resources, and cost.
Learn more: A review of HIPAA-compliant analytics platforms
Piwik PRO vs. Freshpaint
Both Piwik PRO and Freshpaint offer HIPAA compliance, but they differ significantly regarding the provided features.
Piwik PRO is an all-in-one platform with analytics and data activation capabilities that can be further extended through integrations with other tools and platforms. It also employs high-level privacy and security features. Overall, you get HIPAA compliance and full analytics capabilities within one platform.
Freshpaint, on the other hand, doesn’t offer analytics capabilities. It sits between data sources (such as data warehouses) and third-party data destinations and acts as a buffer to prevent PHI from being sent to non-compliant tools. As a result, setup and maintenance require significant technical skills, resources, and coordination across multiple teams, making the tool very resource-intensive.
HIPAA compliance with Piwik PRO
Piwik PRO Analytics Suite allows you to collect and analyze PHI and ePHI, helping you provide an even better and more personalized patient experience while employing the highest privacy and security safeguards. Depending on your organization’s needs, it enables you to track both basic and advanced data.
By signing a BAA with us, you can safely send all types of PHI to your analytics setup. If you prefer, you can de-identify all PHI before sending it to our platform. Either way, you can ensure you stay compliant with regulations.
On top of a BAA, healthcare organizations can benefit from Piwik PRO through the following features:
- Hosting on select HIPAA-compliant Microsoft Azure data centers located in the US
- 100% data control – Piwik PRO doesn’t share or reuse your data for its own purposes
- High-level privacy and security features (compliance with ISO 27001 and SOC 2 standards, including HIPAA certification)
- Granular data access controls to restrict data access only to authorized personnel
- Detailed audit logs to efficiently track data access and changes to the data collection configuration
- Integrated analytics, tag manager, consent management platform, and customer data platform
- User-friendly interface and customizable reports and dashboards
- Integrations with other platforms, marketing tools, data storage and more
- Personalized support and onboarding
After signing a BAA, you can safely use our Customer Data Platform (CDP) and activate the data to acquire new clients, better respond to patients’ needs, improve contact center interactions, and much more.
Best practices for HIPAA compliance in analytics
Healthcare providers must carefully assess and monitor their tracking technologies, what tools can access PHI, and whether they have business associate agreements (BAAs) in place.
Start by reviewing your website architecture, the types of scripts you’re using, and the implementation and settings of your analytics software and tag manager. Consult your legal department or hire an analytics auditor to review your digital infrastructure and determine whether a BAA is necessary.
Consider the following questions:
- Are you tracking user IDs? If yes, how do you use them?
- What data appears in page URLs, titles and query strings?
- What information do you collect in the analytics platform with website forms? How do you use form data in personalization or analytics?
- Have you anonymized/hashed visitors’ IP addresses? Do you avoid tracking GPS or fine-grained location information?
- What other tags and third-party scripts (for example, from your partner’s website) do you use on your website?
Your legal and security teams should monitor changes in HIPAA and other applicable state regulations and guidelines issued by HHS/OCR, the FTC, and others and regularly evaluate your analytics setup for compliance with US law.
Additional security measures include addressing the use of tracking technologies in your risk analysis and risk management processes. To protect PHI/ePHI, implement appropriate administrative, physical, and technical safeguards.
Learn how to ensure your campaigns are HIPAA-compliant: HIPAA, marketing and advertising: How to run compliant campaigns in healthcare.
Final thoughts
The use of Google Analytics by HIPAA-covered entities poses many compliance risks. While it’s technically possible to de-identify PHI and still use Google Analytics, much is at stake. Even minor mistakes can lead to costly lawsuits, civil penalties, and damage to your business’ reputation.
With Piwik PRO, you can apply appropriate safeguards to protect your patient data rather than following a bare minimum approach. We help healthcare companies meet the stringent requirements of HIPAA and offer our clients informative, valuable, and actionable insights.
Learn more about HIPAA and analytics:
- PHI and PII: How they impact HIPAA compliance and your marketing strategy
- HHS guidance on using online tracking technologies: How to make your analytics HIPAA-compliant
- The AHA’s lawsuit against HHS guidance on online tracking technologies: What it means for HIPAA-covered entities and their use of analytics
FAQ
Is Google Analytics HIPAA-compliant?
No, Google Analytics is not HIPAA-compliant. Google explicitly states that it doesn’t satisfy HIPAA requirements, and you can’t use it for any purpose involving protected health information (PHI) if you are a covered entity (e.g., hospital, clinic, insurance company) or a business associate. Google also does not offer a business associate agreement (BAA).
What is a business associate agreement (BAA)?
A business associate agreement (BAA) is a contract between a HIPAA-covered entity and a business associate. It ensures that the business associate understands its responsibilities regarding PHI and will protect it according to HIPAA guidelines. If you want to use a tracking technology that collects and processes PHI, you must sign a BAA with the vendor.
Why doesn’t Google offer a BAA for Google Analytics?
There are two main reasons:
- Data hosting and residency: Google doesn’t offer on-premises hosting or guaranteed data residency. Data is stored in randomly assigned data centers, potentially outside the US, which conflicts with HIPAA’s accountability rule regarding knowing the location of patient data.
- Data usage: Google’s terms allow them to use collected data to develop new services, measure advertising effectiveness, and personalize content. Using PHI for advertising purposes would be a HIPAA violation.
What happens if I pass PHI/ePHI into Google Analytics?
You would be violating HIPAA regulations and Google’s terms of service. This could result in the termination of your Google Analytics account, breaches of HIPAA, fines and damage to your organization’s reputation.
Can I use Google Analytics if I don’t collect PHI/ePHI?
Yes, but it requires significant caution and effort. You must ensure that no PHI/ePHI is transmitted to Google Analytics. Mistakes can be costly. PHI can be found in many different places, including post-login areas, unauthenticated pages, or mobile apps (e.g., in URLs, form fields, or event data).
What is considered PHI?
Protected health information (PHI) is any information relating to a patient’s condition, the past, present, or future provision of healthcare, such as lab or imaging results and medical history, or payment for such services. When identifiers are included in the same record set, PHI becomes individually identifiable health information (IIHI), and it becomes protected when transmitted or maintained in any form by a covered entity. Even seemingly innocuous data like IP addresses, combined with information about a patient’s visit related to a health condition, can be considered PHI.
How can I make my analytics HIPAA-compliant?
- Switch to a HIPAA-compliant analytics platform: The best approach is to use an analytics platform that offers a BAA and provides the necessary safeguards for handling PHI.
- De-identify data: You can attempt to de-identify all PHI before sending it to Google Analytics, but this is a complex, time-consuming, and potentially error-prone process.
- Consider on-premises hosting: Some platforms offer on-premises hosting, giving you complete control over your data and eliminating the need to share it with third parties. However, this option requires significant resources and expertise to maintain data security.
Which analytics platforms offer a BAA?
Analytics vendors that offer a BAA include:
- Piwik PRO
- Mixpanel
- Heap
- Amplitude
- Freshpaint
- Adobe* (for Adobe Customer Journey Analytics but not Adobe Analytics)
The post Is Google Analytics HIPAA-compliant? appeared first on Piwik PRO.
]]>The post Everything you need to know about the New York Health Information Privacy Act (NYHIPA) appeared first on Piwik PRO.
]]>SUMMARY
- The New York Health Information Privacy Act (NYHIPA), passed by the New York Assembly on January 22, 2025, awaits Governor Kathy Hochul’s signature and will take effect one year after signing, introducing stringent privacy regulations for businesses processing regulated health information (RHI).
- NYHIPA applies broadly to entities processing RHI of New York residents or individuals in New York, covering a wide range of data, including health-related internet browsing, wellness habits, and reproductive health information, unlike the more limited scope of HIPAA’s protected health information (PHI).
- The act mandates strict authorization requirements for processing RHI, requiring valid authorization with detailed disclosures and prohibiting authorization within 24 hours of account creation, while also granting consumers rights to access and delete their data within 30 days. NYHIPA also explicitly prohibits the sale of RHI.
- Tools like Piwik PRO Analytics Suite can help organizations balance NYHIPA compliance with actionable insights by offering features like customizable BAAs, data encryption, and granular consent mechanisms, though businesses must also address challenges like the 60-day data disposal requirement and service provider agreements.
On January 22, 2025, the New York Assembly passed Senate Bill S929, also known as the New York Health Information Privacy Act (NYHIPA). The bill now awaits Governor Kathy Hochul’s signature.
The new legislation adopts novel provisions that would make this one of the most stringent privacy laws in the US. It introduces an expansive definition of regulated health information (RHI) and authorization requirements for processing and sharing data with third parties.
If enacted, NYHIPA will become effective one year after signing.
This would make New York the fourth state – following Washington, Nevada, and Connecticut – to impose targeted and comprehensive regulations on consumer health-related information that is not otherwise protected by HIPAA. The act would significantly affect how businesses process health and wellness-related information, including their marketing and analytics practices.
Who does NYHIPA apply to
Unlike HIPAA, which primarily applies to healthcare organizations, NYHIPA covers nearly all organizations that process RHI, specifically ones that:
- Control the processing of RHI of a New York resident.
- Control the processing of RHI of an individual who is in New York at the time their RHI is processed.
- Are located in New York and control the processing of RHI.
Note: Non-NY businesses that process data of NY residents must also adhere to this act. There are no revenue, volume, or nonprofit exemptions.
What is regulated health information (RHI)
NYHIPA protects regulated health information (RHI), which is broadly defined as any data reasonably linkable to an individual or a device that is collected or processed in connection with that individual’s physical or mental health. This also applies to location or payment information and any inference about an individual’s mental or physical health.
NYHIPA regulates internet browsing data, search or purchase histories, data collected through online tracking technologies, wellness habits, and reproductive health information. The definition potentially extends to behavioral data indicating that an individual is seeking health services.
Data protected by NYHIPA vs. HIPAA
Protected health information (PHI) regulated by HIPAA refers to information about health status, provision, or payment for health care that can be linked to a specific individual. This includes records of doctors’ visits, prescription medication details, laboratory test results, insurance information, and others. While the definition of PHI is broad, the concept of RHI is more ambiguous and encompasses even more types of data.
NYHIPA applies to any health-related data that falls outside HIPAA protections, including wellness, marketing, behavioral or employee health data, even if collected by a HIPAA-covered entity.
Regulated health information (RHI) exemptions
NYHIPA exempts four categories of information:
- Data processed by government entities
- Protected health information (PHI) governed by HIPAA and HITECH
- HIPAA-covered entities, but only when maintaining information in accordance with HIPAA rules
- Data collected for clinical trials subject to federal protections for human subjects
- De-identified information – but only if the de-identification satisfies NYHIPA’s specific criteria (technical safeguards, no reidentification, and contractual obligations with data recipients)
The law does not exempt nonprofits, information regulated by the Gramm-Leach-Bliley Act, or public data. Also, HIPAA-covered entities are not exempt with regard to their non-protected health information, such as employee health and wellness data.
COMPARISON
The comparison of 9 HIPAA-compliant web analytics platforms
Compare the main features of Piwik PRO, Freshpaint, Matomo, Mixpanel, Amplitude, Heap, Tealium, Adobe CJA and Piano Analytics.
What are the requirements of NYHIPA
NYHIPA requires valid authorization for data processing, which can include different operations concerning RHI like collection, use, storage, sharing, analysis, modification, or deletion. In contrast, similar laws in Washington and Nevada require consent only before selling consumer health data. Thus, NYHIPA’s authorization requirements are much stricter and more difficult to fulfill.
Processing is allowed without authorization only when it is strictly necessary for purposes such as:
- Providing a requested product or service
- Detecting or preventing fraud or illegal activity
- Protecting vital interests
- Complying with legal obligations
- Internal operations (excluding marketing or advertising)
These activities are explicitly not considered strictly necessary and require valid authorization.
Valid authorization
Regulated entities must obtain valid authorization before collecting or processing regulated health information for something other than a permissible purpose.
Importantly, authorization must not be requested within 24 hours after account creation or first use of a product or service. Organizations must take an additional step to obtain the necessary consent and authorizations during the sign-up process.
A valid authorization must include the following:
- The types of regulated health information to be processed
- The nature of the processing activity
- The specific purposes for such processing
- The names or the categories of service providers and third parties to whom the regulated entity may disclose the individual’s regulated health information, and the purposes for such disclosure
- Any monetary or other valuable consideration the regulated entity may receive in connection with processing the individual’s regulated health information, where applicable
- Notice that declining authorization will not affect the individual’s experience of using the regulated entity’s products or services
- The expiration date of the authorization, which may be up to one year from the date the authorization was provided
- The mechanism by which the individual may revoke authorization before expiration
- The mechanism by which the individual may request access to and deletion of their regulated health information
- Any other information material to an individual’s decision-making regarding authorization for processing
- Notice of prior authorization refusals (cannot request again if authorization was declined or revoked in the past year)
- A signature (which may be electronic)
Regulated entities must allow users to view and manage authorizations in their account settings and enable one-click revocation.
Entities must also publicly post either the authorization form or a representative sample.
Since the authorization expires after only one year, regulated entities need to implement a process for requesting new authorizations annually. Organizations must also allow individuals to revoke authorization for specific processing activities at any time and immediately cease processing their data after revocation.
Authorization requests must be presented in a clear, user-friendly format, free of manipulative interface design (“dark patterns”) that could impair or mislead decision-making.
The requirement to provide tailored forms that track when authorization was given and revoke such authorization after one year is likely to create numerous costly compliance issues for regulated entities. Unfortunately, there is no guidance provided on how regulated entities should verify individuals’ rights requests within the 30-day period for responding, while also implementing measures to prevent fraudulent requests.
Consumer rights
NYHIPA grants consumers the right to access and delete their regulated health information via an effective, efficient, and easy-to-use mechanism through an interface the consumer regularly uses. Notably, consumers may engage an authorized agent to make requests for them. However, the bill doesn’t clarify whether the regulated entities can take steps to validate the requestor’s identity.
Regulated entities must fulfill deletion and access requests within 30 days and pass deletion requests to their service providers or third parties. Deletion by downstream parties must also occur within 30 days unless impossible or disproportionate, which must be documented.
Authorized agents may submit requests on behalf of consumers.
Privacy notice
NYHIPA requires a privacy notice if a regulated entity processes health information for a permissible purpose without authorization.
The notice must disclose:
- The purposes of data collection.
- The names or categories of third parties and service providers that may receive the data.
- How individuals can exercise their privacy rights.
Any material change in processing requires a separate, clear, and conspicuous notice and an opportunity to delete RHI.
Service providers
Regulated entities must enter into agreements with service providers that process RHI on their behalf, similar to business associate agreements (BAA) under HIPAA.
NYHIPA service provider agreements must also:
- Prohibit combining RHI with other personal information
- Require downstream deletion within 30 days
- Require reasonable assessments or third-party audits
- Ensure all subcontractors are contractually bound to equivalent obligations
- Notify the regulated entity before involving further service providers
Penalties for NYHIPA violations
Violating NYHIPA provisions can result in a civil penalty of up to $15,000 per violation or 20% of revenue obtained from New York consumers within the past fiscal year, whichever is greater. The penalty is payable to the state.
There is no private right of action under NYHIPA; enforcement is vested exclusively in the New York State Attorney General.
The Attorney General may bring a civil action to obtain injunctive relief, civil penalties, disgorgement of profits, restitution, and any other appropriate relief.
Although private lawsuits are not permitted, regulated entities should expect active enforcement, especially given recent trends in privacy regulation and litigation strategies targeting health-related data.
NYHIPA vs. other state laws
NYHIPA joins Washington and Nevada in targeting consumer health data beyond HIPAA’s scope, suggesting a national shift toward stricter privacy. It shares significant structural and conceptual similarities with Washington State’s My Health My Data Act (MHMDA), which took effect for most entities on March 31, 2024, and applies broadly to any entity collecting health data of Washington consumers.
Unlike Nevada’s SB 370, which focuses primarily on the sale and disclosure of health data, NYHIPA regulates nearly all types of processing and imposes stricter requirements for authorization, timing, and service provider oversight. Maryland’s new law (MODPA), by contrast, is a general data privacy statute and does not specifically target health data in the same way.
NYHIPA is notable for requiring regulated entities to dispose of regulated health information no later than 60 days after it is no longer needed, which makes it stand out from other state privacy laws. The 60-day disposal requirement poses a challenge, as it conflicts with certain sectoral and legal retention obligations – for example, the New York Workers’ Compensation Board requires some claim-related health records to be retained for up to 18 years. Regulated entities will need to reconcile NYHIPA disposal timelines with those statutory obligations and document any such legal basis for extended retention.
What does NYHIPA mean for covered organizations
Consumers are becoming increasingly aware of how their data is used and demanding greater control over their personal information. NYHIPA responds to these concerns by strengthening privacy protections and restricting the use and disclosure, or sale of health-related data without explicit user authorization. At the same time, it addresses gaps in federal regulations like HIPAA. The impact of NYHIPA will vary between different types of businesses in the healthcare industry.
When it comes to traditional healthcare organizations, HIPAA-covered entities may need to enter into NYHIPA agreements with payment processors (similar to BAAs) to take payments from patients, as payment processors would qualify as service providers. Although traditional medical records maintained by HIPAA-covered entities will likely be exempt, other types of health-related data they collect – such as marketing data, wellness program inputs, or unauthenticated web traffic – may fall under NYHIPA as regulated health information (RHI)..
On the other hand, digital health companies face particularly high compliance burdens, as they often rely on behavioral tracking, personalization, and cross-platform data analytics to deliver services and optimize engagement. NYHIPA’s one-year authorization limit, 24-hour delay rule, and downstream deletion requirements may hinder user onboarding, personalization, and product development workflows.
Companies must analyze online tracking technologies and cookie management tools to determine whether additional disclosure and authorization mechanisms are required.
Given NYHIPA’s expansive definitions, limited exceptions, and strict requirements, all organizations processing health-related information must reassess their data processing and authorization practices. Organizations that have not previously implemented robust privacy-by-design principles – particularly in consumer-facing digital health contexts – will need to accelerate their adoption of data minimization, purpose limitation, and granular consent infrastructure.
The effective date is one year after signature by the Governor, which is an exceptionally short time for digital health companies to implement the required changes. Regulated entities must explore the available methods and service providers, including analytics vendors, that will help them comply with existing and future regulatory requirements.
Selecting vendors that offer robust consent management, transparent data flows, and NYHIPA-aligned service provider terms – such as Piwik PRO – can help organizations balance compliance with actionable insights.
How to prepare for NYHIPA
Digital health companies and other industries targeting New York consumers may find it challenging to comply with NYHIPA. Organizations covered by NYHIPA should begin preparing now to implement internal processes, governance mechanisms, and technical safeguards aligned with the Act’s requirements..
If you are subject to NYHIPA, these are steps you should take now:
- Map your data:
- Conduct an internal audit to identify all sources of regulated health information, how it is used, and where it is stored
- Identify all touchpoints where RHI is processed, including employee wellness data, payment processing, and marketing analytics
- Assess whether data is collected directly from individuals, inferred, or obtained from third parties – and whether it may be linkable to an individual or device in the context of health
- Review all current data uses and eliminate those that are not considered “strictly necessary”.
- Document legal bases for any processing that does not rely on authorization.
- Develop a proper infrastructure for collecting valid authorization:
- Build systems to track when authorization was given and automatically expire authorization after one year
- Implement comprehensive and granular authorization mechanisms that allow individuals to provide or revoke authorization for each use of their RHI
- Ensure no authorization is requested until at least 24 hours after account creation or first use of a service
- Ensure that authorization requests are not bundled with other transactions and are free of dark patterns
- Enable one-click revocation in user-facing systems, including customer account settings
- Establish appropriate agreements with service providers:
- Update contracts to require service providers not to combine RHI with any other personal information received from third parties or from their own relationships with individuals
- Include provisions requiring service providers to notify the regulated entity “a reasonable time in advance” before sharing health information with any further service providers
- Require service providers to allow compliance assessments by the regulated entity or designated assessor
- Ensure all downstream processors are bound by equivalent contractual obligations (“flow-down” terms)
- Include data return or deletion clauses upon termination of services
- Update your technical infrastructure:
- Implement data segregation mechanisms to prevent mingling of RHI with other data sets across services, systems, or clients
- Implement retention schedules that ensure RHI is only kept as long as necessary and securely disposed of after processing
- Create a publicly available retention schedule and securely dispose of RHI within 60 days after it is no longer necessary
- Where longer retention is required by law (e.g., Workers’ Compensation), document the legal basis and applicable time period
- Implement ongoing monitoring and training for employees:
- Provide role-specific training on NYHIPA requirements, particularly for staff involved in product design, marketing, legal compliance, and vendor management
- Establish internal monitoring mechanisms and escalation workflows for handling rights requests, data breaches, or improper processing
Organizations should be prepared for active enforcement once the law takes effect, as regulators in other states with similarly sweeping privacy laws have signaled aggressive enforcement. Even before formal enactment, NYHIPA reflects a broader shift toward regulating non-HIPAA health data, and regulators are expected to scrutinize data practices involving behavioral and inferred health information.
The steps outlined above should become baseline compliance measures for all healthcare companies to prepare for NYHIPA and other existing and upcoming legal requirements.
Supporting your healthcare organization’s compliance journey with Piwik PRO
Piwik PRO offers privacy protection and regulatory compliance while providing actionable insights to improve healthcare services and patient experience.
Here is how healthcare organizations benefit from choosing Piwik PRO as their analytics vendor:
- We will sign a business associate agreement (BAA), allowing you to process any type of PHI safely. If you prefer, you can also de-identify your PHI. Both PHI and de-identified data are exempt from NYHIPA requirements.
- We offer hosting on select HIPAA-compliant Microsoft Azure data centers located in the US.
- We implement the best data security practices, which are validated by our ISO 27001 certification and HIPAA compliance attested as part of our SOC 2 Type II report.
- We don’t share PHI with third parties or reuse it for other purposes.
- We offer granular data access controls to restrict data access, detailed audit logs, regular privacy and security audits, and more.
Want to learn how Piwik PRO can help you comply with healthcare regulations?
FAQ
What is the purpose of the New York Health Information Privacy Act (NYHIPA)?
The New York Health Information Privacy Act (NYHIPA) aims to regulate the collection, sale, and processing of healthcare information. It restricts the uses and disclosures of personally identifiable consumer data related to health and wellness, excluding the protected health information (PHI) collected by HIPAA-regulated entities.
Who is affected by NYHIPA?
NYHIPA applies to “regulated entities” that collect or process “regulated health information” in New York or about New York residents. It covers entities of all sizes, regardless of revenue, processing thresholds, for-profit status, or physical presence in the state.
What is considered “regulated health information” (RHI) under NYHIPA?
Regulated health information refers to any information that is reasonably linkable to an individual or a device and is collected or processed in connection with an individual’s physical or mental health. This includes location or payment information related to an individual’s physical or mental health or any inference drawn or derived about an individual’s physical or mental health that is reasonably linkable to an individual or a device. RHI is not limited to medical records but covers biometric data, genetic information, and even information that could indirectly identify a person.
Does NYHIPA apply to HIPAA-regulated entities?
NYHIPA exempts PHI, not HIPAA-regulated entities. A HIPAA-regulated entity would be required to comply with NYHIPA if they process health data outside the HIPAA definition of PHI.
What are the key requirements of NYHIPA?
Key requirements include:
- Obtaining consent through a transparent opt-in process before selling or sharing consumers’ health data.
- Providing consumers with clear explanations of the types of information collected, the nature of processing activity, the purpose of processing, the categories of third parties with whom the information will be shared, how consent can be revoked, and that use of the product or service will be unaffected by the failure to provide authorization.
- Ensuring consent is obtained separately from any other transaction and only after 24 hours of the first request or use of a product or service.
- Deleting personal data within 30 days of a consumer revoking consent and requesting deletion.
- Processing health data only if it is strictly necessary for providing or maintaining a service or product, with limited exceptions.
- Providing a “clear and conspicuous notice” publicly available on their websites that describes their RHI processing and sharing practices.
What rights do individuals have under NYHIPA?
The Act provides individuals with the right to access and delete RHI. Regulated entities must fulfill these requests within 30 days.
What are the penalties for violating NYHIPA?
Violations of NYHIPA can result in a civil penalty of up to $15,000 per violation or 20% of revenue obtained from New York consumers within the past fiscal year, whichever is greater. The penalty is payable to the state.
Can individuals take legal action against regulated entities for NYHIPA violations?
No, there is no private cause of action under NYHIPA, meaning individuals cannot take legal action against regulated entities for NYHIPA violations. However, the New York attorney general can enforce the law through strict penalties.
When does NYHIPA take effect?
NYHIPA will take effect 12 months after the governor signs the bill into law.
The post Everything you need to know about the New York Health Information Privacy Act (NYHIPA) appeared first on Piwik PRO.
]]>The post The AHA’s lawsuit against HHS guidance on online tracking technologies: What it means for HIPAA-covered entities and their use of analytics appeared first on Piwik PRO.
]]>SUMMARY
- A US district court ruled in favor of the American Hospital Association (AHA) against the Department of Health and Human Services (HHS), stating that HHS exceeded its authority regarding its guidance on online tracking technologies.
- However, the court ruling applies to a specific case and does not vacate the entire guidance issued by HHS. Practices allowed under HIPAA concerning the use of tracking technologies like analytics platforms are still subject to interpretation.
- Healthcare organizations risk violating HIPAA and other laws when collecting and sharing protected health information (PHI) with third-party vendors. They continue to face class action lawsuits, particularly for using tracking pixels that can inadvertently share sensitive patient data with Facebook or Google.
- HIPAA-covered entities must implement appropriate safeguards to ensure HIPAA compliance and maintain patient trust. Particularly, they should opt for HIPAA-compliant analytics platforms and sign business associate agreements (BAAs) with analytics vendors.
Disclaimer: This blog post is not legal advice. Piwik PRO provides privacy-friendly analytics software, but doesn’t provide legal consultancy. If you’d like to make sure that you comply with HIPAA guidelines, we encourage you to consult an attorney.
On June 20, 2024, a US district court ruled in favor of the American Hospital Association’s (AHA) lawsuit against the Department of Health and Human Services (HHS) bulletin on using online tracking technologies, declaring it beyond agency authority. The 2022 bulletin sought to inform entities regulated under HIPAA of their obligations concerning the use of tools like analytics platforms on websites or apps. On August 29, the OCR decided not to appeal the court’s decision.
As a result, healthcare organizations may feel inclined to relax their efforts to ensure HIPAA compliance in their marketing stacks or stop seeking HIPAA-compliant alternatives. However, it’s important to note that the ruling, and HHS’s decision not to appeal, do not diminish the actual compliance risks.
Neglecting HIPAA compliance can damage healthcare providers’ reputations and patient trust, in addition to risking costly fines. Many organizations face class action lawsuits even after the court ruling against the HHS bulletin. Healthcare providers continue to violate HIPAA, primarily through tracking pixels installed on their websites that share sensitive patient data with tech giants like Meta or Alphabet.
In this article, we explain the implications of the ruling in the AHA’s case and how healthcare organizations should use online tracking technologies in ways that let them comply with HIPAA.
The HHS bulletin on the use of tracking technologies
The HHS bulletin was initially issued on December 1, 2022, aiming to address potentially impermissible uses and disclosures of protected health information (PHI) by healthcare providers. According to the bulletin, PHI may be found on many authenticated (password-protected) pages and certain unauthenticated pages and mobile apps, making them subject to HIPAA. For example, the OCR assumed that anyone visiting a covered healthcare provider’s website was, is or will be a provider’s patient.
Learn more: HHS guidance on using online tracking technologies: How to make your analytics HIPAA-compliant.
The AHA lawsuit against HHS and its guidance on tracking technologies
In November 2023, the American Hospital Association (AHA), joined by the Texas Hospital Association, Texas Health Resources, and United Regional Health Care System, sued HHS to bar enforcement of a rule adopted in its bulletin on the use of online tracking technologies.
The AHA challenged the HHS’ interpretation of HIPAA requirements, especially its overly broad conception of PHI. They argued that, contrary to HHS guidance, a person’s IP address combined with a visit to a specific webpage isn’t sufficient to constitute PHI.
The AHA stated that the HHS bulletin upended hospitals’ and health systems’ ability to share health care information with the communities they serve and analyze their website traffic to enhance access to care and public health. The AHA also argued that essential website tools like analytics platforms will no longer appear on hospital websites. The AHA’s lawsuit was supported by 17 state hospital associations and 30 hospitals and health systems.
After the original bulletin was challenged in court, HHS issued revised guidance on March 18, 2024. The revisions, however, left regulated entities with the seemingly impossible task of distinguishing between what is and what is not a disclosure of PHI subject to HIPAA based on a website visitor’s intent. The AHA called the modifications “cosmetic” and stated that “the modified Bulletin suffers from the same basic substantive and procedural defects as the original one.”
In June 2024, a judge ruled in favor of the AHA, declaring that the OCR had overstepped its authority when issuing the guidance. The ruling centered on the interpretation that an IP address combined with website visit data from an unauthenticated page does not constitute PHI. On August 29, the OCR announced it would not appeal the district court’s decision.
The impact of the court ruling on HIPAA-covered entities
The court ruling and HHS decision not to appeal it do not mean that the issue of protecting PHI in the context of analytics tools has been settled once and for all. The ruling was issued in a specific case, indicating that an IP address combined with visit data from an unauthenticated web page does not constitute PHI. However, the ruling does not vacate other parts of the guidance, like those relating to authenticated pages such as patient portals. HHS can enforce certain instances of combining HIPAA identifiers with health information – for example, an ad click ID connected with a scheduled doctor appointment shared with an ad platform like Google.
The HHS is not the only authority governing HIPAA compliance. Even if data doesn’t fall under HIPAA, it may still be subject to other privacy regulations. The Federal Trade Commission (FTC) has issued orders in several cases relating to healthcare providers, and it’s not directly tied to HIPAA. A common legal basis for the FTC’s involvement is the FTC Act, which prohibits unfair or deceptive trade practices. In April 2024, the FTC ordered the telehealth company Cerebral to pay a $7 million fine and limit the use of consumer health data for advertising purposes.
Collecting and sharing PHI still requires special caution
While the court’s verdict in AHA’s lawsuit may serve as a benchmark for later decisions on possible HIPAA violations, the complexity of PHI protection and the diversity of contexts involved dictate particular attention. The fundamental issues surrounding the collection and use of PHI by healthcare organizations remain unchanged.
What is allowed under HIPAA concerning the use of tracking technologies like analytics platforms continues to be subject to interpretation. While the definitions of PHI and ePHI are well-established, the widespread use and interoperability of modern IT systems make it alarmingly easy for PHI to inadvertently leak into your website or app. Therefore, it’s wiser to stay on the safe side rather than rely on a gray-area interpretation of PHI that maintains the status quo.
The rise in class action lawsuits against healthcare providers
In recent years, dozens of class action lawsuits have been filed against healthcare providers across the US. Most of these lawsuits concern the providers’ use and sharing of patient data with major ad platforms.
Two Louisiana health systems – LCMC Health and Willis-Knighton Health – were sued for using Meta Pixel on their websites, which shared medical data of hundreds of thousands of patients with Facebook and Instagram. Advocate Aurora Health agreed to pay $12.2 million to settle a lawsuit for disclosing the personal health information of more than 2.5 million people to Meta and Google without their consent.
The ruling in the AHA’s case does nothing to protect healthcare companies from these class action lawsuits, especially since they allege violations of state and federal privacy laws, such as the California Consumer Privacy Act (CCPA) or the Illinois Biometric Information Privacy Act (BIPA), not HIPAA. Many states have laws that protect the same information as HIPAA and provide a private right of action, which HIPAA does not. The class action lawsuits indicate that healthcare providers continuously fail to sufficiently protect patient data from being shared with third parties.
Focusing on patient trust
Consumers have grown more aware of their online privacy and how their personal data is being used, and this trend will only increase. People don’t want to be tracked by ad tech companies, especially when it concerns their health information. But, as we can see, many healthcare providers continue to neglect patient privacy by sharing their sensitive information with third-party vendors.
Healthcare companies also struggle to adequately inform consumers about the use of third-party tracking technologies on their websites. A recent study of 100 US hospitals found that 96% of hospital websites transmitted user information to third parties, and only 71% had a publicly accessible privacy policy. Of those, only 56.3% disclosed the specific third-party companies receiving user information.
Considering all these aspects, the AHA ruling does not remove healthcare organizations’ responsibilities when collecting and sharing sensitive patient information with tracking technology vendors. They must apply proper safeguards to protect themselves from costly lawsuits and civil penalties. Let’s not forget the root of all this – patient trust – which means there is no room for bare-minimum measures in protecting patient privacy.
Here is what you can do to ensure your use of analytics stays in line with HIPAA requirements.
How should healthcare organizations comply with HIPAA and HHS guidance
Healthcare providers must carefully assess and monitor the tracking technologies they use, what tools can access PHI, and whether they have business associate agreements (BAAs) in place.
On top of that, they need to monitor any future guidelines issued by HHS/OCR, FTC, and other state privacy developments in this space.
HIPAA-covered entities must sign a business associate agreement (BAA) with a tracking technology vendor that meets the definition of a business associate before passing PHI to them. If you can’t sign a BAA, you must adequately de-identify PHI or restrict its flow to analytics.
HIPAA-covered entities must ensure that all disclosures of PHI to tracking technology vendors are permitted by HIPAA. Using any PHI/ePHI for marketing or advertising without a BAA can be a severe violation of HIPAA.
Consider the following cases:
- You need BAAs for tools containing user data, such as CRM systems and customer data platforms (CDPs).
- You might not need a BAA if your analytics tool runs on unauthenticated websites.
- You must sign a BAA if your analytics tool runs on authenticated (password-protected) pages, such as a patient portal.
However, these approaches heavily depend on what data you collect on respective pages. If any data, even that collected on unauthenticated pages, could be used to identify an individual and relates to their health, it could still be considered PHI. You must carefully assess all data collected, regardless of whether the page is password protected. Consult your legal department to review your digital infrastructure and determine whether a BAA is necessary.
While a BAA ensures that the vendor complies with HIPAA, it does not eliminate the need for patient authorization. Covered entities must obtain written authorization from patients before using or disclosing PHI for marketing purposes, as well as for selling it. This includes any campaign that promotes a product or service, especially if it involves payment. However, authorization isn’t required when the activity is related to treatment, payment, or healthcare operations.
Valid patient authorization under HIPAA must be specific, informed, and given voluntarily, and must include the following:
- The specific purpose for which the PHI will be used, such as analytics, research, or improving patient care.
- The types of PHI that will be collected and used such as IP addresses, search queries, or appointment details.
- Any third parties, such as analytics vendors, that will receive the PHI.
- An expiration date or event after which the consent is no longer valid.
- How patients can revoke their authorization at any time.
- Signature and date by the patient or their legal representative.
A consent management platform (CMP) can help you automate the process of obtaining, managing, and tracking patient consent.
Read more: 45 CFR §164.508: Requirements for authorization in marketing and other non-TPO disclosures.
What if you can’t sign a BAA with the analytics vendor
Without a signed BAA with the vendor, healthcare organizations must de-identify PHI using one of the approved methods:
- Safe Harbor method: Remove all 18 identifiers listed in HIPAA (e.g., names, addresses, dates, Social Security Numbers) and ensure no remaining data could identify an individual.
- Expert Determination: Engage a qualified expert to confirm that the risk of re-identification is “very small” using statistical or scientific methods.
Once de-identified, the data is no longer PHI and can be used for analytics without a BAA.
Freshpaint is an example of a platform that adopts de-identification. It uses techniques such as creating anonymous visitor IDs and irreversible cryptographic hashing to de-identify data. Freshpaint’s key feature involves preventing PHI from being shared with non-HIPAA-compliant tools
However, de-identification is challenging and requires significant resources to do it properly. Despite efforts to de-identify data, there remains a risk that sophisticated technologies could re-identify individuals, especially if the data is combined with other datasets. De-identification requires careful handling to ensure the data remains protected and useful for analysis, which can be difficult to achieve in practice. On top of that, managing de-identified data with a platform like Freshpaint requires coordination between legal, technical, and marketing teams.
Another option for healthcare organizations to mitigate the risk of HIPAA violations is data anonymization. For example, they can use third-party anonymization software to irreversibly mask PHI before transmitting data to analytics vendors. You need a signed BAA with the anonymization vendor, but since the analytics vendor does not receive PHI, you don’t need a BAA with them.
Anonymized data, while offering maximum privacy protection, may not be suitable for all types of analysis or research. Anonymization reduces data accuracy and granularity, strongly limiting its value. Achieving proper anonymization requires advanced techniques and thorough validation.
Companies can also use HIPAA-compliant “limited data sets” (retaining some identifiers like dates) for analytics if a data use agreement is in place. This avoids a BAA but still requires contractual safeguards to prevent re-identification.
Aggregated data for healthcare operations, such as population health analysis or quality improvement, is permitted under HIPAA if the BAA with the business associate explicitly allows it. Without a BAA, aggregation alone is insufficient unless combined with de-identification. For example, combining de-identified datasets from multiple sources to analyze trends without exposing individual identities.
The most secure approach for HIPAA-covered entities involves switching to an analytics platform that explicitly supports HIPAA compliance and provides appropriate safeguards for handling sensitive health information.
The biggest web analytics providers, Adobe and Google, have not changed their guidelines for using their most popular products: Adobe Analytics and Google Analytics 4. Adobe and Google will not sign a BAA for the use of these platforms, both of which are not designed to be HIPAA-compliant out of the box.
HIPAA-covered entities should not use those products.
Learn more about how popular analytics vendors approach HIPAA compliance: A review of HIPAA-compliant analytics platforms.
HIPAA-compliant analytics with Piwik PRO
Piwik PRO offers an all-in-one analytics platform consisting of four integrated modules – Analytics, Tag Manager, Consent Manager, and Customer Data Platform. As a healthcare organization, you can use our comprehensive features to build a powerful, HIPAA-compliant analytics stack that includes data collection, analysis, and activation.
We are committed to providing HIPAA-covered entities with the most secure marketing platform. We help companies in the healthcare industry meet the stringent requirements of HIPAA and offer our clients informative, valuable, and actionable insights.
We will sign a BAA with you, allowing you to send all types of PHI to your analytics setup. If you prefer, you can also de-identify all PHI before sending it to our platform.
Other HIPAA-related features that are part of our product include:
- Hosting on select HIPAA-compliant Microsoft Azure data centers located in the US.
- ISO 27001 certification.
- HIPAA compliance attested as part of our SOC 2 Type II report.
Learn more: Piwik PRO is officially HIPAA certified!
- Granular data access controls to restrict data access only to authorized personnel.
- Detailed audit logs to efficiently track data access and changes to the data collection configuration.
- Not sharing ePHI with third parties or reusing it for other purposes.
- Regular privacy and security audits by external, independent bodies to ensure the highest level of security measures.
After signing a BAA, you can safely use our Customer Data Platform (CDP) to deliver trusted and personalized healthcare experiences. CDP empowers you to unify patient data from different sources, remove data silos, and create a secure foundation for driving effective marketing and communications and improving your services. You can activate the data to acquire new clients, better respond to patients’ needs, improve contact center interactions, and much more.
If you want to learn more about how Piwik PRO can support you in providing better patient experiences while maintaining HIPAA compliance, reach out to us:
The post The AHA’s lawsuit against HHS guidance on online tracking technologies: What it means for HIPAA-covered entities and their use of analytics appeared first on Piwik PRO.
]]>The post Piwik PRO is officially HIPAA certified! appeared first on Piwik PRO.
]]>As such, we are pleased to announce that a HIPAA (Health Insurance Portability and Accountability Act) compliance assessment extended our SOC-2 Type II audit and was positively approved. This means we are officially HIPAA compliant. In receiving this recognition, we demonstrate our commitment to safeguarding the data we collect and the high standards we have set for ourselves.
What is HIPAA certification
HIPAA certification refers to the process by which organizations comply with the US Health Insurance Portability and Accountability Act (HIPAA). This federal law protects sensitive patient health information from being disclosed without the patient’s consent or knowledge. An external audit examines a company’s adherence to HIPAA rules and evaluates the organization’s controls related to security, availability, processing integrity, confidentiality, and privacy of PHI.
Achieving HIPAA compliance involves several steps to ensure that the organization meets all the requirements outlined in the regulations. These include developing policies and procedures, implementing security measures, and creating a comprehensive business associate agreement (BAA).
If you want to learn more about HIPAA read:
- A review of HIPAA-compliant analytics platforms
- HHS guidance on using online tracking technologies: How to make your analytics HIPAA-compliant
- HIPAA, marketing and advertising: How to run compliant campaigns in healthcare
- The AHA’s lawsuit against HHS guidance on online tracking technologies: What it means for HIPAA-covered entities and their use of analytics
Why HIPAA certification matters
Obtaining HIPAA compliance certification will further enhance our compliance with healthcare data protection standards.
You may also like:
At Piwik PRO, we are committed to providing healthcare organizations with the most secure marketing platform available:
- We help companies in the healthcare industry meet the stringent requirements of HIPAA regulations and offer our clients informative, valuable, and actionable insights.
- We exclusively partner with select ISO 27001 and SOC2-certified Microsoft Azure HIPAA-compliant data centers.
- We operate following the best data security practices. Clients from industries handling sensitive data, like healthcare, are a prime testament to our expertise. With Piwik PRO, they have the flexibility to either de-identify all PHI in their data or sign a business associate agreement (BAA) to ensure that the collection and processing of PHI and ePHI comply with HIPAA requirements.
- We provide granular data access controls to restrict data access only to authorized personnel. Piwik PRO also maintains detailed audit logs to easily track data access and changes to data collection configuration.
HIPAA certification proves that Piwik PRO Analytics Suite is a verified solution for customers whose policies mandate partnering exclusively with HIPAA-compliant vendors. This certification demonstrates our commitment to ensuring a HIPAA-compliant analytics suite safeguarding Protected Health Information (PHI). Consequently, our future and existing clients can have greater confidence in the security of our data handling processes.
Want to learn more about how to make your analytics HIPAA-compliant?
We’re here to help and answer all your questions!
The post Piwik PRO is officially HIPAA certified! appeared first on Piwik PRO.
]]>





